Join our discord to talk with me and others about the episode: https://discord.gg/qHsqhW62
This week, I'm going to change up the format a bit. I'm putting you in the seat of a hacker as they start their journey. Ever wonder how they got your email address? What kind of stuff they might need to get into your account and how they can get it just by doing a little bit of google-fu? Come with me this episode while I take you on that tour of Open Source Intelligence, some presidential blunders that can come from it, and what Skip Tracing is.
And make sure to check out @shell_pod on Instagram or Twitter for more informaton. You can also email me at shellpod@protonmail.com
We've had a lot of talk on the show about command line heroes and villains. Hackers that use exploits, that spend their time scanning and looking for holes in the network to wiggle their way in and bring down their foe. What if I told you, that one of the biggest threats to your network didn't need a vulnerability in microsoft, or apple, or google to get in. What if I told you that all they needed….was you.
I'm John Kordis, and today I want to take you on a trip where you don't need complex code or a library of exploits to get what you want. You just need patience, smarts, and to know where to look. So come with me and take a look at What the Shell open source intelligence is and what hacks wouldn't have been possible without it.
This episode is going to be a little bit different than some of the last few. I'm going to start out doing a bit more of a conceptual dive into a few topics, and then I'm going to tell you how they've been used in a few big time hacks. We're going to put you in the mindset of a hacker at the start of their attack to begin. Let's start with some broad strokes first.
And to do that, we'll start at square one of our fake attack. How do you think that they get information on you? How do they know that your email is right or that this is going to even get delivered? There's a stage in every hack at the start called "reconnaisance". In short form, it's just gathering the information needed to get started. This reconnaisance can be done on two sides, the scanning side which we won't go into, and the open source side. Open Source intelligence is any kind of information that is freely available to the internet at large, if you know where to look. It's also reffered to as OSINT, so if you hear me say that going forward, just know that this is what I mean.
So in this instance, for a future attack, we might say: "Alright, I want to hack into Chicken Jaw productions. I'm going to first look them up in google and linkedin. On LinkedIn you'll be able to find at least a partial list of employees. With that list of employee profiles, you can probably correlate it back to at least a few different facebook profiles. After all, not everyone has theirs set to private, and there's informaton that you can use to tie the two together. For example, if both profiles have the same job, or profile picture, or location? Now you've got a much bigger picture of just who these people are and you might even have some more identifiable stuff like phone numbers listed on their profiles.
If you're an attacker, you're building a profile of all these people that you've got so far. And in those profiles might be things like keywords. Those keywords are all derived from stuff that you might have posted, or liked on your profiles and they all paint a very tiny part of the picture that is, well you. They can be used to do things like guess passwords or the answers to security questions. So for example, myself. Someone might take my likes: hacking, marvel, cats, security, Dresden Files, stuff like that. And plug it into a tool that creates varying attempts at passwords around them. If they're able to do so, they might even go to my facebook and see what I'm commenting on, and if I'm doing anything like answering those quizes or question posts that seemingly circulate around for no apparent reason.
From there, what we call your attack surface is growing. Now, maybe someone in linkedIn also had their work email broadcast as a part of that? Boom, you've got an email structure against the company. You might know that the it looks like the emails are first initial, last name, @ the company name because you found bburns@chickenjaw.com.
So we've got a small platform of information at this point and a more clear picture is starting to form. We might at this point take a look at public breach information. Public breaches. Do you remember all the way back in episode 1, when I told you that the root cause of the Colonial Pipeline hack was a re-used password? Well, a lot of the time, when hacks happen, there's dump of usernames and passwords, or valuable credentials like even credit card numbers. I can almost guarantee you that you've gotten an email saying you've been involved in a databreach at somepoint and this is the kind of stuff they take. Well, if it's not publicly posted by someone, it's gonna be privately sold. In fact, most of the time, they're just a google search away.
There's a saying in IT, "google is your friend" and that's really true. But sometimes it can be your enemy too. I'm going to run you through one example right now. I'm just searching my own old email address that I decommissioned a while back. And do you know what I found? A post on a forum where people sell usernames/passwords, stolen credit card applications, database dumps, and more. It's a public site where if you're a member you can sell your services for hacking for the right price or buy a tool like an ATM skimmer! It's not even concealed behind the dark web. And in that post, there were hundreds of emails and passwords, some of which included students, some of which were clearly work emails. And you know why this site is still active? It again, goes back to something we talked about in episode 1. It's hosted in Russia. So, we can't explicitly get it taken down here, and as mentioned before, if it's not doing direct harm toward the Russian Government, we're unlikely to see any real action being taken against it from that side either.
So if you're an attacker and you're lucky, you might be on your way inside an account with just what's available on public sites.. Let's bring this up to an example at a real high level. Let's say…a presidential level.
I'm going to rewind a bit here to 2016. Just before the election. A Dutch security researcher by the name of Victor Gevers, had a thought. "Would it be possible to log in to a candidates twitter by password guessing". Gevers job is to disclose vulnerabilities so that people can fix them responsibily. He's done this hundreds of thousands of times and ultimately done quite a bit of good through the procees. Well, the question he was asking now was a fair one, after all these are people that would be steering the course of a nation and if their account was easily accessible, what would stop hackers from potentially doing something terrible with this ability. So, they chose a target. The, at the time, presidential candidate, Donald Trump. At this point he's probably best known for two things, his long standing television show "The Apprentice" and speaking out about his displeasure with the current administration.
Gevers went to work creating a small profile of password guesses, not really expecting to get anywhere. He guesses the first one. Nothing. Second one. Nothing. A few more and no luck. But on number five, something unexpected happens.
Audio of Trump saying "You're fired"
Yep, on guess number five, with the password 'yourefired' he got in. No caps, no special characters or anthing. This was his signature catchphrase, so it's not like it would have been far down the guess list at this point. However, the two surprises there are that there was no special character or numbers here, it was the most basic a password could be, and even more striking is that there was no 2 factor authentication. That being a secondary code that needs to be entered on the account in order to log in, to prove that you are beyond a doubt the owner of the account.
Gevers didn't really know what to do, he got in but wasn't quite sure how to responsibly disclose this one. If he did it publically it would be inviting others to try and they'd likely get in just as easily. So he resported it to his local authorities. He even included a list of suggested passwords like "maga2020!". Which, honestly wasn't much better but it definitely was a step up and in the right direction.
Well. Years later, in fact, just over a year ago now, in October of 2020. Gevers decided to give it another go. It was just before the 2020 election and I suspect he had a similar thought of "can't happen twice, right?" Well. Fortunately this time it was not yourfired anymore. But the password that used this time? maga2020!.
The president had this to say:
Audio of Trump claiming that a hacker needs a certain percentage of your password and an insane IQ to hack you.
Sorry, but this was just incorrect. This is the leader of the free world and his password was guessed using nothing but public knowledge about him. That's the kind of thinking that OSINT thrives on in order to drive exploitation.
After this issue, Gevers emailed a division of Homeland Security dedicated to Cybersecurity to make them aware and the presidents password was changed pretty shortly after. In addition to that, this actually launched a bit of a change in how twitter handles security for high profile individuals, no having more strict requirements for passwords and security.
For those listening at home, I hope you have a bit more clarity now on how easy it can be. Let's move on to the other big topic, which is phishing.
You probably know about phishing at this point. It's when someone sends an email to you and it has a link that's specially made to trick you into entering something like your personal info or to get you to download something you're not supposed to. It's one of the biggest problems out there because it's insanely easy to do and the attackers don't really care if they get your email address wrong as long as they get some of the ones on their list right.
While we're on the topic of presidential compromise, let's see how easily a phishing email can snowball with Hillary Clinton.
Back in that 2016 election, a major issue came to light when it became clear that personal email systems were being used for government purposes with regard to the clinton campaign and positions. That's not really what we're going to discuss here though. What we want to know is how one phishing attempt gave way to another presidential level compromise.
Earlier this episode we talked about the reconnaisance phase. Where we did all that research. Well, in March of 2016, Russian hackers did just that, except instead of a company they targeted the Democratic National Committee. Within a week of the operation beginning many of the members received this email, that read:
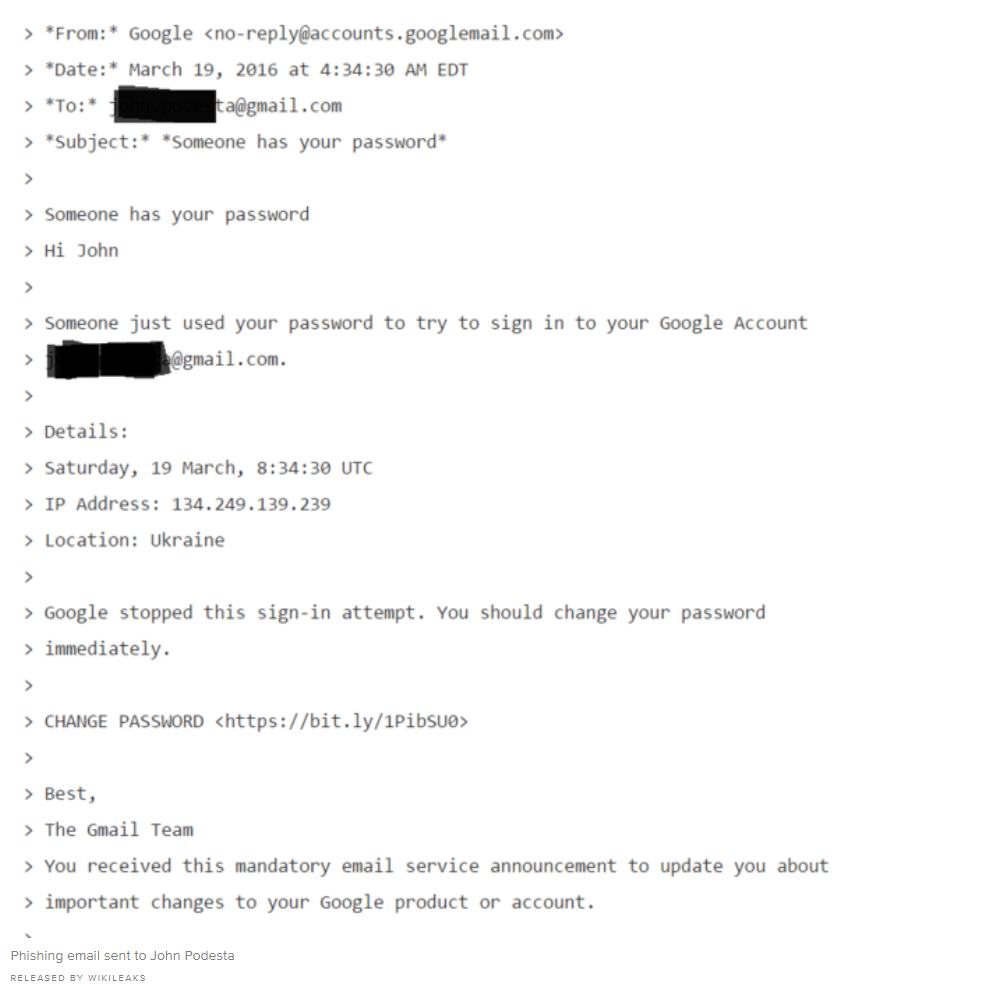
One of the recipients of this message, was John Podesta, the former White House Chief of Staff and Counselor to President Obama. To their credit, whoever maintained that email went to confirm and was sent the proper link to change Podesta's email, but instead clicked the malicious bit.ly link instead.
That bit.ly link, was a link to a fake google password change, which would ask for a current password, and a new password. That single link, would spawn what were known as the Podesta emails on wikileaks, a series of emails that made it obvious that government discussions were taking place on personal email infrastructure.
This particular attack was caused by the group designated Fancy Bear, a russian threat actor known for attacks targeting journalists, the olympic committee, and dozens upon dozens of military targets.
The attacks didn't stop there, they were expanded on to target more and more members of the democratic party. It's a major snowball effect where just one click on a link led to what was arguably one of the biggest blows in a presidential election to date.
Phishing might seem like it's a bit of a joke, especially when most of the time it comes as spam like shopping or sex sales. But when it's directed right at you, it can be the tip of a long and dangerous spear.
These attackers, that use all the informaton they can gather from the public eye, aren't just relying on major exploits to get in, they're relying on you. They take the small things, that you might not think are important and use it to paint what ends up as a clear picture.
I want to bring it down a little more street level though now. Because in addition to the big groups that are looking to make a buck off you clicking a link there's more close to home stuff. Because it turns out, there's plenty of room in the law for these kinds of activities if you do it right. Open Source Intelligence is pretty frequently used to do things like track down people fleeing from court and even catch online predators. This type of position is often called a "Skip Tracer"
One guy, named Alex Price, has actually made a great cause out of it. Alex is one of the most well known skip tracers in the world, going by the alias SkipGuru. He's got over 30 years experience and started by simply tracking down people who weren't making their car payments. But now, he helps participate in a program called The innocent lives foundation. This program is aimed at taking down online child predators through the use of open source tools and technologies. Since they became a thing, they've taken down over 250 predators.
Other pretty common uses for Skip Tracers? People who flee court hearings. You can essentially think of them as digital bounty hunters! One such bounty hunter? A woman by the name of Michele Gomez.
When Gomez was a child, her parents insisted that she channel some of her time into learning the ins and outs of computers, even going to far as to built one from scratch including down to soldering the connections together. She likens her online bounty hunter to the construction of a motherboard, stating that "“Profiling a subject is a lot like constructing a motherboard, You have to see connections that are invisible to other people by filling the spaces between with information.”"
And see those connections she does. In one such case, she retrieved both a missing yacht and a criminal wanted by the FBI. Back in 2013, she had been contracted by Alternative Collection Solutions to recover a 53 foot yacht called the morning star. It was missing about a year at this point, allegedly in the possesion of a man named Ryan Eugene Mullen. Mullen, being wanted for stealing over 2 million dollars from federal agenices, was a bit of a high profile target, but an elusive one as well. So, after talking it over with feds, her potential pay for this bid was 10k from ACS and the criminal reward money for catching Mullen.
Gomez started by searching the traditional methods, of Shelter, Income, Transportation, and Social Contact. If you could hammer down some of these points on someone you had a good lead. Unfortunately, using the social security number given, Mullen had done a good job at obfuscating his record with fake names and addresses. Eventually though, through tracking a litany of name changes and potential points of contact. He and the boat would be caught by Gomez. In fact she had caught him securing the yacht on his way out as a couple of scam real estate transactions had fallen through. And after cuffing him up and getting him over to the authorities, she managed to get the boat released to her that same day to bring back to ACS. It's certainly an exciting field to be in from time to time. But there does seem to be a bit of a spectrum where the exctiement can exist.
Now I've told you a bit about some of these jobs and the people behind it. But I've actually got something interesting for you all. Next week, my normal off week, I'm going to be releasing an interview with an actual Skip Tracer. You might recognize the name Cyber Sector 7. I've posted a few times about him and his podcast where he dives deep into the open source watering hole and how he's currently tackling digital privacy. I don't know his real name, so for this We'll just call him "Tank". It's his alias that I know him as and I think it suits the situation fine. Tank is has done the job and I'm going to dive a bit in with him and hopefully have some interesting bites for you to take next week.
For now, I'm John Kordis. And thanks for listening to me tell you about Open Source Intel and social engineering are. I'm looking forward to getting you all back here next week for the bonus episode.
Hey you, if you're reading this and want a secret role on the podcast discord, message this to me privately on discord
“He felt that his whole life was some kind of dream and he sometimes wondered whose it was and whether they were enjoying it.” and what it's from.

