This week, we're going to dive into the full story of the guy that stopped Wannacry; Marcus Hutchins. Trust me, it's worth the listen.
Store: https://store.whattheshellpod.com
Discord: https://discord.gg/mBPbWcVRYR MalwareTech: https://www.malwaretech.com/
Marcus Hutchins Documentary: https://youtu.be/vveLaA-z3-o
Last episode, we dove into a crazy story about zero days, black market exploit dealers, and how crippling one piece of malware can be to an entire section of industry. If you haven't listened to that one yet, I suggest you do because it does tie in pretty heavily to todays episode. We also went a little bit into the details about how it was stopped, and more importantly, the man that stopped it; Marcus Hutchins. But, as with most great stories there's more to Marcus than just this event, a lot more. I'm John Kordis, and today I'm going to take you on a bit of a dive into Who the shell Marcus Hutchins is…..cyber hero or dark net genius and leave it up to you to decide for yourself.
In the hacking community, you often find people lumping themselves into a few categories. There's the black hat, those are the cyber criminals, people that hack for malicious purposes or at least perceived malicious intent. A lot of time it might really just be people hacking out of curiousity but it always boils down to the fact that there was never legal permission given to these people. Then there's the white hat, the people that get paid to do this for a living and have the legal permissions and authority to do so. Those are your red teamers, pen testers, security researchers. Anyone that does it within a legal scope can fall under this umbrella.
But what about if you started at one end of the spectrum and ended up on the other side. What if you thought about you were doing good by revealing vulnerabilities but you didn't stay within the lines. What if your life was a little bit gray? As with most things, it's easy to see the binary of it all but lets step back today and as I'm telling you this story let's thinking about the gray.
When we left off last week Marcus Hutchins has triggered the killswitch to the wannacry ransomware. That was in 2017 but I'm going to take you back a bit so we can really understand who Marcus was at this point in his life.
Hutchins was born in 1994, in Bracknell England. That's about an hour and a half outside of London proper. His mother Janet was a nurse and his father Desmond, a social worker. There wasn't anything here really remarkable about the family, and that's how things would stay for Marcus.
As Marcus grew up, he started showing the similarities we see with other people like Mitnick or Jonathan James. The early fascination with computers and technology. Growing up a bit ahead of him, it's really easy to see why this generation took to it too. It felt kind of like we were growing up with technology. Windows kept evolving, the interenet and access kept changing, and so did we as kids learn to grow with it.
Now, Janet Hutchins had a computer back at home, that had Windows 95 on it, this would have been around the year 2000 or so. Over the years Marcus would install whatever programs he found interesting, occasionally take the machine apart, and soon just develop an overall curiousity with the world of computers and programming.
Even before the age of 13 Marcus was using programming to do, what I would call, exploit development. Like most of us growing up he had a computer class that largely consisted of learning to type. Marcus, already being pretty well versed in typing had found this kind of class a bit beneath him and started setting out on finding ways he could avoid doing the work. What he found, after a bit of exploration was that in Microsoft Word there was an ability to write code in a language called visual basic that could be attached to word documents. This was primarily used in enhancements to the documents but, being the ever clever teen he was Marcus decided to code his way out of his boredom.
Step one, use this capability to get around the blocks on installing software. Since the code to download and install likely ran at a different permission level and outside the bounds of the blocks in place this meant all he had to do was choose the right program to install. So what did he choose? A proxy. The proxy would, in effect, bounce whatever web traffic he wanted to browse through another address. That meant that none of the blocking rules would be an issue anymore and while his classmates were typing away, he could do whatever it was he wanted to do.
And with wins like this, his love of computers would only grow. He'd use similar techniques to thwart his parents attempts at putting parental controls in place time after time. When their parents couldn't do anything on the computer to block him they tried the router, only to fail there as well.
As he grew into his teens, Marcus did what a lot of us did growing up in the age of the internet. He found a community. Where he found it was a forum dedicated to learning hacking and expanding the knowledge. People would share what they were working on, and this really fell into the gray area of hacking because while you could in theory assume that some of this was done on personal systems and as tests, in reality when you see forum topics like "botnets" things start to get a bit off.
But, in spite of that, Marcus still being kid took all of this and wanted to really apply it. He was in awe at all the things coding and programming could do. One of the first projects Marcus would end up creating to show his skill? A password stealer for internet explorer. You see back around 2008, when Marcus was 14, internet explorer was starting to be able to store your passwords for you. Microsoft tried to keep things proper with this, they didn't just store your passwords in plain text. What Marcus was able to steal was a bunch of encrypted passwords.
Marcus though, well he was starting to show signs of his innate capability for reverse engineering. That's taking programs, code, malware, and really figuring out how it worked and the intricacies of their internal processes. We saw him do it last episode on Wannacry. Well, when he looked into Internet explorer, what he found was the location of the decryption key used to move the passwords from that encrypted status into plain text. So Marcus in this case had found the locked safe and the key. It was met with some immediate praise and Marcus wasn't really using it for bad purposes. It seems like, at least based on his interview with Wired, that he was just testing whether or not he could do it.
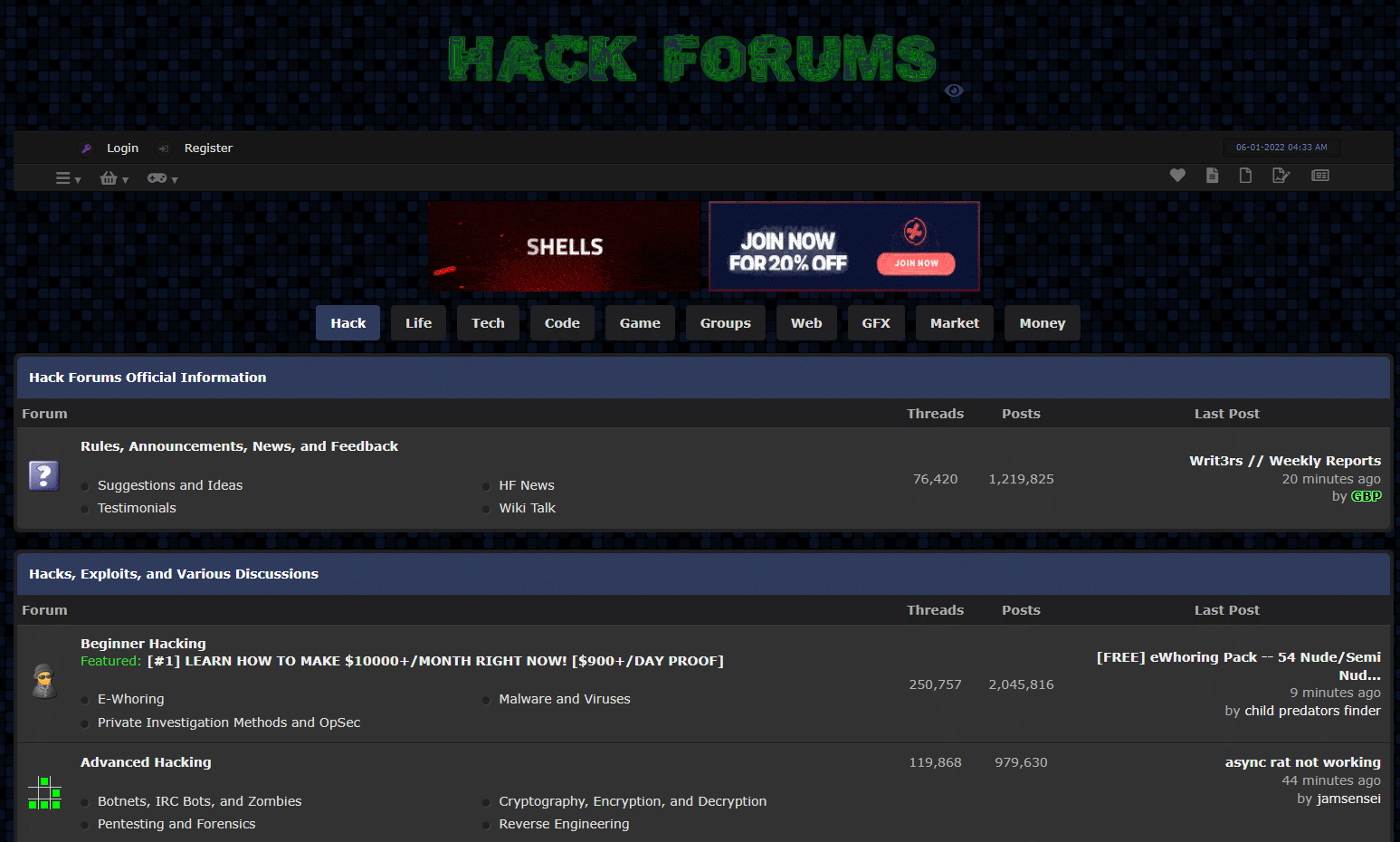
If I'm correct in reviewing some of the sources for this, the forum he was actually a part of was called HackForums. Now, this site has been around for a while. I remember looking at the site and being a bit intimidated when I was in high school and trying to grasp some fundamentals. Now, is the site inherently bad? Not really. Some of the topics range from learning the basics of wifi hacking, to things like advanced forensics and penetration testing. That doesn't change the fact that illegal dealings did happen from time to time on the site. Between 2013 and 2018 there have been at least 10 instances of malware either being developed or sold before use on the site. But without getting into the ethics of whether or not every user is bad because of this I just wanted to lay the groundwork so you understood what kind of site this was. I've even got a screen shot of the home page on my podcast transcript at whattheshellpod.com. Or, if you're feeling daring, you can even just go there right now. The site is up and running!
Over the coming years Marcus kind of developed this routine where he'd submit work to the site, maybe pull some examples to work from, and then even sometimes use for examples or homebrew solutions on his school network. In fact, it seemed that he had made enough waves in the school he attended that the IT department knew him by name. Eventually, after allegedly causing an incident resulting in the need to replace one of the school servers, Hutchins just kind of stopped going when he could. Some times he wouldn't go, and when he did he'd show up as late or leave as earl as he could. Instead opting to spend his nights learning to hone the craft of coding and malware development.
So, here we are at 2009. At this point Marcus is just 15 years old and he's on hackforums bragging about his escapades. One of the bigger brags he'd made came in the form of him saying that he'd created a botnet of 8000 computers that he could use.
Now, for anyone that isn't aware, think of a botnet as a group of computers that can all be used by a common owner. You can tell all 8000 machines to say, start flooding a website with requests and shut it down by way of a denial of service attack. The fact that it's 8000 different machines makes it harder in this case to block the attack. Another way you might want to think about it? A hivemind with Marcus at the center. He's able to tell these "bots" to do whatever he needs to make his projects easier.
The botnet he'd created actually seems to have involved little work on his end. Once he created the base code for it, he'd just disguised it as an alluring torrent that someone might want to seed and download, then let it spread from there. He could switch it up to make copies for more torrents if he wanted but that's really the base of how it spread to the 8k machines.
But as the botnet grew, and he even made a bit of money off this and renting out servers to his community, so did his boredom with what he was doing. Was this really all he was going to do? Add to the botnet? Be a glorified dark web landlord? Ultimately, he decided he was done with this side of it, and wanted to go back to his root. He wanted to do a bit more development.
Some of the earliest work he did at this point had landed him enough attention that he started taking on requests for malware development contracts on HackForums. The tools he created ranged from things that would be able to tell you if anti-virus was able to defend against a particular malware, and what's called a rootkit. Rootkits in this case being a piece of malware that has full admin level permissions on a device and is designed to run as stealthily as it can to try and hide it's own presence. Since the quote root level permissions let users alter or edit log files, this can be pretty easy and make them hard to detect. Hutchins' rootkit sat in the shadows and watched you enter data into forms on websites. You know, forms that might have something like say a username or password field? At it's core level this was a stealth credential harvester.
Well, his reputation was starting to be legit on the forum and eventually a guy that went by the name of Vinnie reached out to Marcus with an intriguing offer. He said to Marcus that he wanted a rootkit and that he'd make Marcus some money for it. But, in this case, he wasn't buying up front. Instead he'd take this rootkit to sites that would pay miles above what HackForums users might pay and then give Marcus a cut of each sale. It seemed like a more well thought out approach to Marcus who ultimately saw in Vinny someone that knew what he was talking about. So that's how at 16 years old, Marcus got to work developing what was called the UPAS Kit.
Upas was crazy. I spent quite a bit of time looking at the code for this rootkit and reading writeups to try and be able to break it down for you and I'm still not sure I get the complete ins and outs. All you need to know is that this thing was adaptive. It had ins and outs to keep it on the system and reinstall if something found it in one location. It could adapt based on the different kinds of operating system architectures that were out there, and it worked well. This versatility and reliability were big in getting it to sell.
This rootkit was called Upas after a tree that's sap was often used to line poison darts and arrows. The analogy works here because this thing was pure poison on the infosec community at the time.
This ended up being the start of a budding friendship between Vinny and Marcus. But while Marcus wasn't exactly sure if Vinny was this persons real name, eventually the same wouldn't be said for him. Vinny was able to get Marcus to give him his name and address under the lure of a birthday present that would be sent to him.
And to be fair, he got quite the bit of a gift. Imagine, if you will, what a box of goodies would look like if it was sent from a drug dealer. Weed, mushrooms, ecstacy, all stuff that's highly addictive, rather illegal, and now looking pretty appealing to a 17 year old kid.
All in all, they worked together to craft upas over a 9 month period and it made Marcus a good chunk of change. Enough that, for him, Marcus had decided he was going to just drop out of school and play the crypto markets with the money he had.
I want to stop here for a second and get an idea of where your heads at. Because if I was listening to this right now, it'd be really easy for me with the benefit of hindsight to say this kids an idiot, why didn't he get know he was getting played. But remember he's just 17. He's a kid that has not really had the most social of lives, and finally found something he was good at. Something that, in all likelihood no one in his circle would understand. Now he's found out that not only is he good enough to have a reputaton but he can make money and even friends online doing it. It's just…it's just easy to look from outside in and condemn the behavior when you aren't the one that walked the path. So let's keep that in mind.
Vinny, seeing potential profit in Marcus, wasn't done though. Maybe the drugs were actually his way of giving a gift, maybe it was just to get Marcus's info, maybe it was to force a dependency on him. Either way, it was pretty clear the Vinny saw Marcus as a way to keep the money flowing. And Marcus didn't quite figure it out yet, but Vinny had him under his thumb.
It wouldn't take too much longer for that to become apparent though. Because Vinny came back a knocking asking Marcus to develop part of a new piece of malware that was to become upas 2.0. But, Vinny was really putting the emphasis on the 2.0 here. He was asking for more features, promised more money, and was really pushing all the stops out here.
Here's what some of the new features would end up being:
The first, a keylogger. After all, if you can get every key that's pressed then you've probably got some usernames and passwords in there. But that would take some creative filtering because think about every key you press on a day to day basis, and every time you type. Then multiply that by thousands. Not only is that a lot of data to store, it's a lot to sift through and search for.
So what else does Vinny ask for? He wants some fake text input boxes. Imagine, if when you're logging in you see something like "enter username", "enter password", "confirm password". You might be keen to enter the password. But that second box, that wasn't anything other than a collection point for your personal information. So now, we've got your password handed over on a silver platter! That might not be the exact context in which this feature would be used but it's certainly one of the possibilities. He wanted to insert fake boxes onto websites the victim would visit, in what are called Web Injection attacks.
This, would make Markus concerned because this type of attack, in addition to credential theft, had a very scary secondary association, bank fraud.
A threat actor could potential get around 2 factor authentication by presenting the victim with a fake code box for their authorization code. Then, if they were close enough in timing, use that code themselves with the compromised credentials from the keylogger.
Initially, Marcus declined to work with Vinny on this one. It seemed to high risk. Not only was the association bad, but this would be something orders of magnitude greater in terms of illegality than he'd done before. So, when Marcus decided this was a no-go, that's when Vinny played his hand.
Vinny, would choose this moment to remind Marcus of the all the illegal work they'd done up to now, and then insinuate that if Marcus didn't work with him on this, that his real name, address, and some details on upas might make their way to federal agencies.
Checkmate. Vinny had Marcus where he wanted him, and Marcus….not really seeing a way out of this, went with it.
If you listen to interviews with Marcus, I think he views this point in particular as a huge crossroads in his life. A point that he knew would come back to haunt him but that he was being forced to take the road that would lead him down a dark path.
Either way, over the next few months Marcus wrote upas 2.0. Vinny, during this time chose to rebrand the tool. Instead of just making another upas, he'd aggregate all the different aspects of the rootkit that he was contracting out to different malware authors, do the QA himself and eventually in June of 2014 put what would be known from then on as "Kronos" into the public for purchase.
During that period of Kronos development though, Marcus had tried going back to school and enrolled in a community college. But once Kronos launched there would inevitably be more work for him in the form of fixing small problems with the malware. So now life became a balancing act, on one end of the plank was finishing his community college degree and on the other was keeping up with Kronos, which don't get it twisted, was still making him a fair bit of money.
The drug problem only got worse in this period too. He'd started to feel an immense sense of paranoia that any minute the cops could be coming for him for his role in all this. Not only that, to keep up with both sides of his life, he'd upped his drug use. That drug use kept him in the frame of mind to go on days long coding binges, and continue to get his school work done.
Eventually, Marcus would start to drift out of the Kronos part of his life and make a new friend who went by Randy. Marcus had refused to write banking malware for Randy but still kept communication. The difference this time was that Randy was as open about his life as Vinny was secretive. It came as a nice change of pace for Marcus, and offered what looked like a more sincere friendship at a point in his life where it was needed.
To keep money flowing Marcus had effectively automated his use of cryptocurrencies by choosing the right points to buy and sell. While he wouldn't write malware for Randy, he did eventually begin to trade crypto for him, starting with an injection of 10,000 US dollars into the crypto market.
Things went well between the two until the summer of 2015 when an electrical outage knocked out the system Marcus was trading from, resulting in the loss of around 5,000 dollars out of Randy's savings. As a way to make amends for this Marcus decided to give Randy a copy of Kronos for free. Randy, finally getting his banking malware, called thigns square between the two.
So now, let's flash forward a little bit because right around here is where Marcus starts working overtime to get his life in order a bit. He quits drugs, cold turkey as a matter of fact. It was, however a months long endeavor. And once his brain got into a stable enough point he decided to get back into the world of hacking but not as a criminal. This is the point where he decided to make use of a blog he'd started a few years prior, a blog I talked about last episode. A blog, called MalwareTech. He used the blog to publish malware analysis papers, and other topics he found interesting in the community. It grew to a pretty decent follower count as well, especially as he started publishing deep dives on some of the biggest botnet players at the time. He'd gone so far as to infiltrate these botnets, and learn where the hijacks machines were. In doing this, he'd be able to develop a tool that would let you actually track the botnet like you were tracking the spread of a disease.
Now we're at the point where Marcus's work in the legitimate side of thigns paid off because at this point, the CEO of a cyber security firm out of Los Angeles contracted him to make their own version of the botnet tracker, a firm names Kryptos Logic. Not only did he follow through with the tracker for the Kelihos botnet, but he'd better a second one as well, to track another botnet, the Sality botnet.
The genius in Marcus wasn't lost on the company and they made him a job offer. A six figure salary reverse engineering malware and aiding the company in their efforts to provide security to their customers. He'd accept the position and continue working there for quite a bit. Now we're up to the point where I tell you again, if you haven't listened to the last episode on Wannacry, go do it.
Because Wannacry is what took Marcus's reputation and gave it a massive boost. After all, being the guy that stopped what was possibly the most high visibility ransomware attack that's ever been seen meant a lot of attention. His follower count on social media skyrocketed to over 250k, currently it's sitting at just over 300k.
So it was no surprise that when he went to defcon later that year that he was treated like royalty. And he really did live it up out there. Defcon is a pseudo underground conference for hackers and the community that happens every year in Las Vegas. It's a major event for the industry and for people that want to learn more. You'll find a lot of people on both the black hat and white hat side of things here. If you ever go, be very careful of where you connect your phone or computer to.
So he shows up, he's treated like royalty, effectively parties the whole week. Then…on his way back home to the UK something strange happens. Listen to him tell the story. This snippet is taken from a documentary that's free to watch on youtube. It's called hacker:hunter - Wannacry: The Marcus Hutchins story. It's about a half hour long and absolutely worth the watch. I'll be linking it on my site and in the description if you want to take a look. But anyways, let's listen to Marcus tell this part of the story
Yeah. It seems like Kronos came a knocking here. To him, he had on some level known this day was coming for a while. But the interesting thing here was that no one else did. So when the community saw him arrested everyone suddenly assumed that this was because of his work on Wannacry. The whole hacker community rallied behind him, getting him gofundmes, crying against the DoJ on twitter, and some even going so far as to launch retaliatory ddos attacks.
Not everyone was keen to think him so innocent though, for a hot second there was even speculation at this point, that he'd made Wannacry himself but it just got out of hand.
After posting a 30,000 bail and being separated from all his technology Hutchins had to use his counsel to manage legal funds for his case. That legal fund being in part, the funds raised by the community. However, since this was the hacking community it would come out that not all these were legitimate donations, and some were made by stolen credit cards. So that money ended up being returned and wiped from the fund altogether.
It ended up being that the money that posted his bail came at the behest of two people in the industry; a married couple Tarah Wheeler and Deviant Ollam. Neither of these two had met Hutchins before and had actually just left Las Vegas. But Wheeler, with a nice severance package from Symantec, decided that instead of a down payment on a house, they'd use that money to bail him out. So they ended up on a plane back to Vegas to help Hutchins. According to them in an interview with Wired, they saw quote "young, foreign, nerdy person of color being held in federal detention,” saying that “He was the closest thing to a global hero the hacker community had. And no one was there to help him.".
Here in the story, Kryptos Logic would put him on unpaid leave. He's still stateside and would stay that way making his way out to Los Angeles on savings. He's talked in interviews at this part of his life about the tremendous guilt he'd had. I understand legally he probably had to take the bail here. If he didn't, it would seem like maybe he was admitting guilt on some level. But he'd been riding the reputation of "cyber hero" for quite a while.
Well, after nine months of living stateside after his arrest. Nine months where he spent a lot of time thinking about what this meant to him and who he wanted to be coming out of this, he would be presented with a deal. In the Spring of 2018, the deal stated that if he gave all the information he had about everyone who he worked with on the Kronos malware and his time spent working as a malware crafter for hire, they'd give him no prison time on his sentence.
He cooperated to the best of his ability, but obviously he never really found out who Vinny was. So that was a bit tough. Along with this, he'd still land with a few felonies and would also post an online confession on malwaretech and one on twitter.
The one on malware tech reads a bit more formal titled "Legal case update" and saying that quote:
"As you may be aware, I’ve pleaded guilty to two charges related to writing malware in the years prior to my career in security. I regret these actions and accept full responsibility for my mistakes. Having grown up, I’ve since been using the same skills that I misused several years ago for constructive purposes. I will continue to devote my time to keeping people safe from malware attacks."
Where the one on twitter, gave a bit more insight into how he really felt deep down. That one read “There's [a] misconception that to be a security expert you must dabble in the dark side,” Hutchins wrote. “It's not true. You can learn everything you need to know legally. Stick to the good side.”
So what's he up to now? Honestly not much different than before. He's still at Kryptos logic. In the court hearings the judge made note of the fact that it seemed like Marcus had turned away from this road quite a while ago. Not only that but that he'd done an immense amount of good for the community since. I like to think that Kryptos Logic saw the same thing and kept him on because of that. He's still active on twitter and on youtube. He's got a lot of interesting videos breaking down major exploits and vulnerabilities.
All in all, he came out of this about as clean as he could have. It does leave you with some interesting things to think about though. Was he purposely walking that dark path? Or was he pushed, inch by inch, until he turned around and found that he was so far into it he couldn't see a way back? How much of this was young naivity and how much was just a bit of greed and ego boosting? What would have happened if he'd refused to help with Kronos back then, or if he'd never responded to Wannacry? Would he have even been anyone of interest to land on a radar in law enforcement?
I don't know, but it's interesting to think about. Let me know what you think on any of my platforms because I'd like to get your take on it. That's it for this episode, I'm your host John Kordis, thanks for listening to me tell you What the Shell happened with Marcus Hutchins.
hanks again for listening to this weeks episode. As always, if you liked it please leave a rating or a review. Or, if that's not something you really want to do just recommend it to a friend maybe? I'm still a small show so word of mouth goes a long way. If you want to come and talk to me directly, along with other fans, I've got a link to our discord in the description and on the website. I'd love to have you other there. It's also a great way to just give topic suggestions. If you listened to last weeks trailer, you might have heard me say that this season is going to try to take you, the listener, into account a bit more. Like I said last week, the idea for the Wannacry and Marcus Hutchins episodes came from my friend in the UK, Rav. So thanks for that Rav. I hope you liked it. And lastly, like I said, I've got a store now, so if you want a sticker for your laptop, a patch for your backpack, or maybe just a T-shirt, go take a look.

