We're going back to North Korea this week with an episode that does a bit of a dive into their internet structure, so you can see how someone recently decided they had enough with their phishing tactics and took it down. Check out ancillary images and details at https://whattheshellpod.com and follow me @shell_pod on twitter and instagram for more content too!
Intro
There have been a few episodes where we've talked about when Nation State actors like Russia or North Korea go up against companies or bigger targets. We've discussed what it means for Russia to have targeted the Colonial Pipeline, or for North Korea to target Sony Pictures. But what about when they go up against the cyber community at large? When there's no specific target, but the web is wide and they're hopeful that they'll catch something.
What would happen if in looking for for swordfish, they pulled in a shark instead? This week, we're going to talk about what happened when one man was targeted by a north korean phishing attempt. The caviat? That man was a cyber security researcher and had decided he had had enough. Who is he? What did he do? Well, we'll get to that but for now I'm John Kordis, and I'd like to invite you this week to join me while I tell you What the Shell happened to piss this guy off, and how he took his revenge.
North Korean Internet Structure
Before we get into the attack, I need to contextualize a couple of things about North Korea's internet structure and some of their phishing strategy that led to this.
When you think about the internet, where does your mind go? For some of you it might be to social media sites, news outlets, or streaming services. Maybe it's a way to get your app online and interact through that. Most of my listeners live in a pretty lucky and time and place if you're listening to my show. The internet, while somewhat regulated, is still relatively free range. If your activities aren't illegal odds are you'll have no qualms about being able to host a platform to promote what you love. At the highest level, our internet providers open the door to the internet at large, and on the other side of that door is an ever evolving tree of branching roads to different possibilities. We have services and tools on the backend that you've likely never seen or interacted with before allow you to navigate that road and that host the destinations at the end of the path. They'll route the traffic from your phone or computer all the way to the end where you might be trying to find a reddit server or youtube page, each of which has been assigned it's own public facing IP address. There are only a finite number of public Ips available because of how we structure them, and I won't go into too much beyond that but to say that with the current standard we are allotted 4,294,967,296 and these addresses are bought and allocated to avoid having issues where multiple people try and use the same ones.
It's because we have all these different possibilities for hosting and the freedoms to choose that we're able to have as much as we do. But what if that was locked down and owned entirely by the government.
Well in North Korea, instead of comcast or warner, they have Star Joint Venture Co, which is a joint company in part owned by the NK Government. And through this they own about 1024 public IP addresses. By contrast the United states has over 1.5 billion. And while it's estimated that there might be more addresses, the estimated number of actual internet users is no more than a few thousand. This is based on the fact that outside computers are illegal, and the Morning Panda company that produces North Korean computers makes no more than a couple thousand per year.
In context, unless you're in a core privileged elite or working as a part of the government or state media, it doesn't seem likely that the interenet is something you're accustomed to here.
That whole connection, comes through one line that runs from Pyongyang, the countries capital, through the mountains and into China. This single line infrastructure means that connections are likely slow, but also that since they control the gateway in, they'll be able to control what people inside and out see of their own networks. That's in part why it was so easy for them to block Facebook, Youtube, Twitter, and other sites they deem to be capable of spreading quote "misinformation" to their citizens.
Back in 2016, North Korea made a mistake with their name severs, which are essentially the maps to the roads we were talking about early. A name server says 'oh you're looking for youtube.com? Take this path' and points you to the right address. Well, sometimes an attacker will attempt what is called a dns zone transfer is designed to make replication of the information stored on those maps easy for redundancy. But sometimes if it's not configured right the public can sneak in and perform one of these to get a glimpse at all the possible sites and destinations that are there. From the outside it was found that only around 30 websites are accessible to the world at large. Here are a couple of them, and I should emphasize that you can go visit these now. There's nothing illegal or blocking you.
- Air Koryo - A flight ticket sales site
- cooks.org.kp - A culinary resource site
- kcna.kp - A north korean news website
- korfilm.com.kp - The website for the Pyongyang International Film Festival
- and ryongnamsan.edu.kp - The website the Kim Il Sung University.
It's likely a very careful presentation designed to give us a curated glimpse at a slice of life in North Korea, but it's still eerie when you think of just how few websites we can see. There is also an internal network that we can't see that likely has a more widespread scope but that's only accessible if you're on the North Korean net already so we don't have as close a glimpse into as we do to this side of things.
North Korean internet goes down
The reason why I wanted to contextualize how small the North Korean is for this is so that you understand exactly what I mean when I say "The North Korean internet was brought offline". In my research there are likely three instances in which one might see an article titled "The North Korean internet has gone offline" .
The first, is a manual shutdown of the routers that control traffic in and out. Routers aren't just for your home afterall, your businesses and countries all have routers that direct and control traffic. So, if Kim Jong Un and the government over there ever decided that they didn't want us to see those websites, or they didn't want their elite to see the outside world? Well it would be pretty easy to give the order to sequester themselves off from the internet at large.
The second, is a hardware glitch. There are a great many companies that don't do business with North Korea. That includes tech companies and networking companies too. That means, that they need to rely on what might not be optimal tools to manage their equipment and that may, in fact, be prone to failure. It's something that happens everywhere, but with limited resources the downtime might be more substantial in a case like this if something failed hard.
The last one, would be a cyber attack. It's technically possible to launch either denial of service, infrastructure based vulnerability, or a myriad other cyber attacks at the North Korean infrastructure and have some level of impact. Some of these outages have, after all, been relatively close in time frame to alleged hacks against US companies from North Korean actors, so it's hard not to see it as a potential retaliatory slap on the wrist. But the US government isn't the only one that might do it. After all, there are many many many hacking groups, and even individuals that might want to target them.
And this is where we're gonna want to keep an eye on, that last sentence. Because in January of last year North Korea went on a little phishing expedition against the security industry at large.
One such Scam happened early last year in 2021
We've all seen phishing scams in the past. One common way that people will try to phish is to pretend like they belong. You might get an email from someone posing as a coworker or a superior. I know in my experience, I've had emails allegedly from my C level executive, but that came from a gmail account. Those kinds of things become immediately suspicious. But sometimes, the technique works.
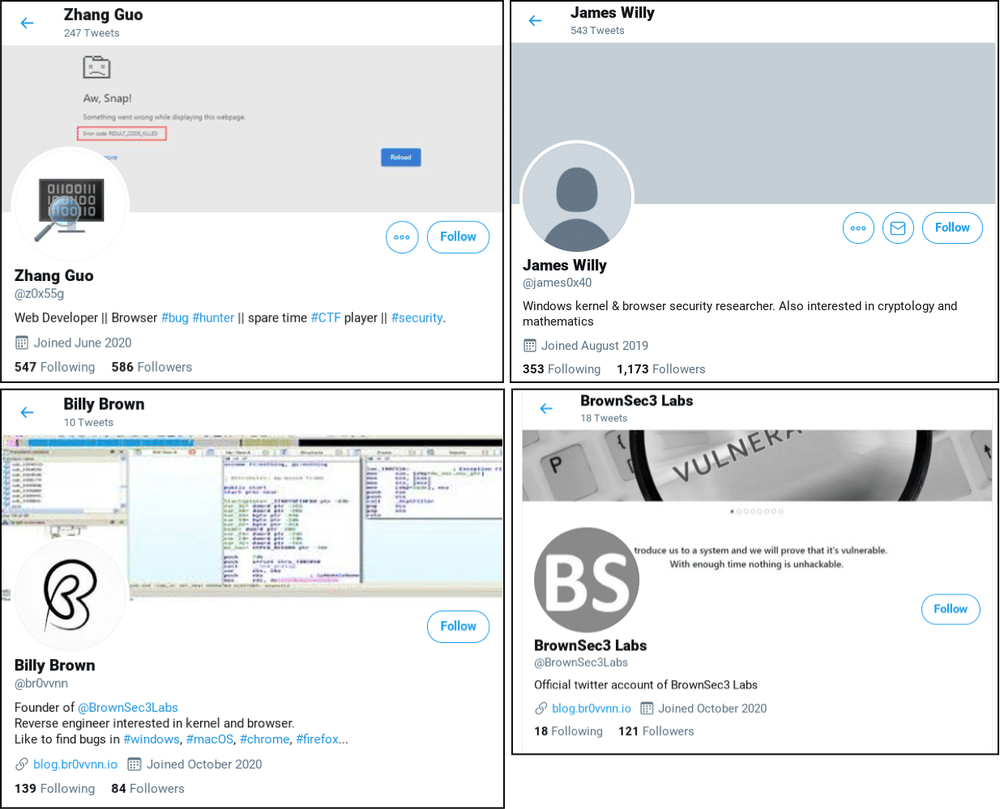
Well, in 2021 North Korean hackers tried something similar. Back in January of that year, google noticed something. Their threat analysis group noticed that security researchers that had a history of vulnerability detection and exploit development were being targeted for information on sites like twitter. And, In doing some recon on the accounts, it was found that this was a front that went beyond the social network.
A blog was created, twitter profiles for fake researchers, even youtube videos detailing their alleged exploits were all created to lend credibility to the idea that these people were legitimate. So that when the time came and they reached out to you, it would seem like they were members of the community.
It was truly incredible because if you went to their blog, the site had entire writeups, and even quote "guest" articles.
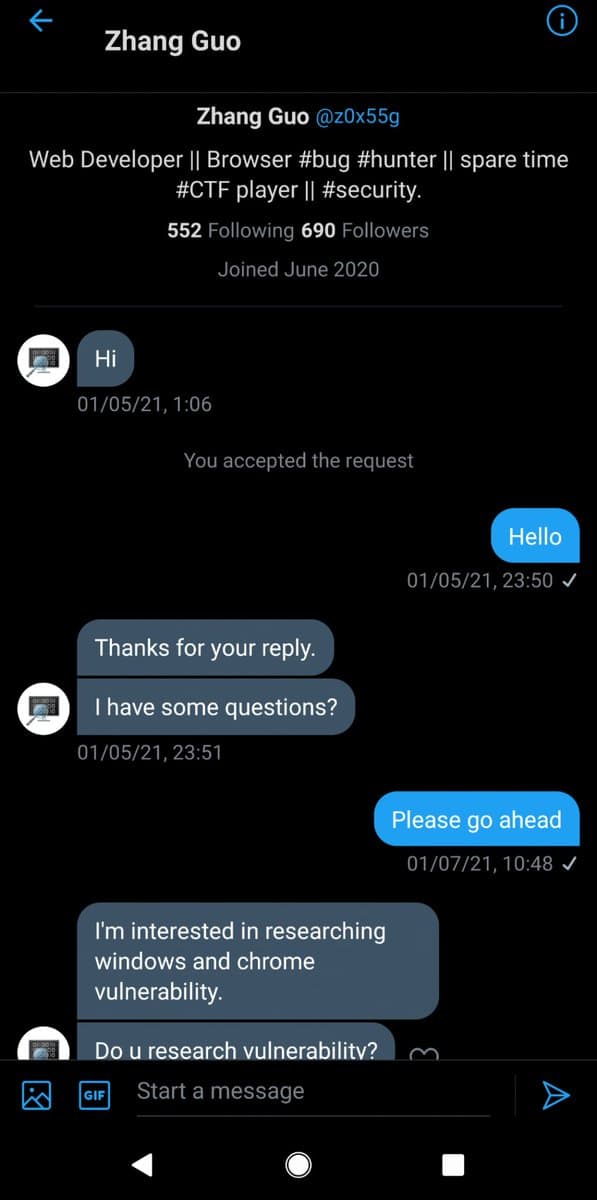
With the front set up, the fakers would now reach out to legitimate researchers to follow through on the end game. I've got screenshots of some of the messages sent on my website, but it went like this. If I were an exploit developer, I'd get a message just saying something like "hi" and asking if I'd be able to answer some questions. Then they'd go one to ask if I'd be interested in collaborating or helping them learn about windows and chrome vulnerabilities.
Eventually, if I agreed, they might send me their own code to compile or look at. This is where they'd strike because on the surface it would be a package that can be opened in Visual Studio which is a tool used for code development. However, there was also a little bit of malware hidden in the package that was meant to establish a connection to the hackers endpoint.
That connection would have allowed North Korean actors to gain access to the system, and potentially pillage any exploits or research that had been done, which was their end goal here. It's like they're trying to steal trade secrets so they can get the one up on the community before the disclosure goes public.
It should be noted though, that it's not just twitter that was used. They used LinkedIn, Discord, email, and more. But one thing that any good researcher, coder, and especially anyone in the field of exploit dev knows is that you don't just run code given to you. You look at it closely because this kind of thing happens a lot where the code says it does one thing, but it might also have that little extra bit that could do you in. If you do want to run it even after that, you do it on a secluded system so that it doesn't come anywhere near anything of value.
Well. As these little phish attempts were happening. It turned out they targeted one guy who decided that maybe he wanted to take some action in retaliation.
For the duration of the podcast I'm going to refer to this guy as his handle online, P4X. That's P-4-X here. P4X was one of the people that was a victim to the January phish attacks. And while he managed to prevent any kind of swiping of his tools and work, it left a bit of a chip on his shoulder. That chip grew as his resentment toward the nation state for exploitation of a community he loved, only became larger. So earlier this year in 2022 he decided to do something about it.
So Pax decided to take some of the action that we've talked about time and time again. He started by scanning what we new North Korea had for internet facing stuff. This is something that anyone can do but if you did it incorrectly, it would be incredibly easy to get in trouble, caught, or even just had your traffic dropped. Well, he landed with a bit of a jackpot. Several of North Korea's only internet facing routers had not been patched for a vulnerability where he could easily perform a denial of service attack against them.
This meant that with the right exploit code, he could knock down the routes from the external internet into the North Korean internet. So Pax got to work, automating everything he could using the vulnerabilities he found, to consistently take offline the sites he could and the routers he could. In an interview with wired, he shared that it was surprisingly easy from his side to do this. With his work, almost every one of the sites we talked about earlier this episode was down for almost two weeks. Not just the sites though, because with taking down these routers you also took down their ability to route things like email and other traffic in and out of the country. It was a bit of a heavy blow back even if it was an easy blow.
Pax had this to say in that interview too, about why he did it. Quote
“It felt like the right thing to do here. If they don’t see we have teeth, it’s just going to keep coming,” says the hacker. (P4x spoke to WIRED and shared screen recordings to verify his responsibility for the attacks but declined to use his real name for fear of prosecution or retaliation.) “I want them to understand that if you come at us, it means some of your infrastructure is going down for a while.”
And I get it, if you don't stand up to the bully, the bully keeps coming right? Actions have consequences and coming after the community known for securing networks and applications was sure to come with some big ones if they ever decided to band back.
I personally think what he did was pretty interesting because it kind of brings to light how much of an impact one person can have on something that isn't given proper upkeep in the cyber domain.
But, let's talk about the other side of the coin here. Because while being a bit of a cyber vigilante might seem like it's a cool day for Pax. Like real vigilantism there are drawbacks.
I want to talk a little bit about 2 possible impacts that could have come from something like this. The first is that it could have interfered with already underway intelligence operations. It's a bit of a trope in TV right, the cops bust a drug ring, and suddenly one of the guys reveals he's an undercover and you just ruined a two year operation!
That's an incredibly simplistic approach here, but it's still possible that cyber vigilantism like this could do something like that. Imagine if there was data exfiltration that intelligence agencies were relying on during that time, and now that's come to a halt. It could have real impact if something like that was interrupted.
Moreover, what if intelligence agencies were keeping those vulnerabilities in their back pocket to use as well. A less likely case here since these were not unknown vulnerabilities, but it's still something that could have tipped off North Korea into their lagging infrastructure and triggered change that would impact the big three lettter agencies abilities to get in.
The other major possibility is diplomatic relations. And this is something I find myself thinking about a lot these days. Because, while Pax was not acting on behalf of his country, that does not mean that NK would not hold the country accountable for it's citizens. It's not like we have the most stable relationship with North Korea as is, giving more ammunition to destabilize it is a bit of a risky game. And it's not just North Korea. In the past month and a half, I've talked pretty openly about how the cyber community is rallying around the Ukraine to help it survive the war thrust upon it.
Some of the reaction that we've talked about included hacker groups taking a vigilante approach against Russia and Vladamir Putin. The response has been amazing to see and it's incredibly interesting, but it's scary when you consider that if one got too far, and attribution was forwarded to a country that it's very possible it could have real kinetic impacts on the war. There have already been stern warnings about western interference with the war, and a cyber interference isn't unexpected but I imagine that the responses are very carefully laid out to keep within a scope that won't have real world blowback to the originators. If someone else came in and launched a more destructive attack, who knows what kind of reaction would be expected.
I don't know what the right action is. I understand people wanting to help and doing it the way they know how. It's easy to feel powerless, and by taking back some level of control and inflicting a little damage it can be a way to show strength. But I also know that we have an incredibly deep and intelligent suite of agencies and cyber warfare units that are almost certainly taking action as well. I don't know where people should realistically draw this line, but it's just something I've been thinking about lately.
Pax admits, he had no interest in full on destructive capabilities here. When wired asked what he was looking to accomplish? He came back with quote
“Regime change. No, I'm just kidding,” P4x says with a laugh. “I just want to prove a point. I want that point to be very squarely proven before I stop.”
and I think he did prove a point. It's good that it was proven, but I wonder if he not only stood his ground, but paved the way for someone who might want to take it a step further next time. We often think about cyber security in the binary of safe or exploitable, but there's also a layer of ethics and laws to consider when something reaches that exploitable stage. As Jeff Goldblum once said, people can so preoccupied with could do something, they don't stop to think is they should. It's a question I encourage you to think about as well.
I'm John Kordis, and thanks for listening to me explain a bit of cyber vigilantism. I'm back from a bit of a hiatus I took recently and we'll be releasing on the normal schedule now. I've been pursuing some certifications for work and that took up a bit too much time for me do both the show and the that. As always you can check out the accessory images on the website at whattheshellpod.com or follow me at shell_pod on twitter or instagram.
If you want to debate cyber ethics with me, you can also head to our discord. The link is on my website and I'm always around to talk about the episode and answer any questions you might have!