This week, I’m doing a bit of a timetable of what the cyber conflict side of the Ukraine-Russia War really looks like through this year. Please consider donating to these groups to help
https://voices.org.ua/en/donat/ https://donate.wck.org/give/236738/#!/donation/checkout https://razomforukraine.org/donate/
For the transcript please visit https://whattheshellpod.com
Intro
So far on the show, we've talked about famous hackers, hackable devices, how some countries can make money off cyber-attacks, and how some just use it as a response measure. This week I want to talk about something that you'd have to be living under a rock not to already be aware of. We’re going to talk about Russia. More specifically, we're going to talk about how they're fighting this war not just on the physical front, but how they've been coordinating cyber-attacks to coincide with their operations. It's a hybrid war, and it may shock you to learn what some of these tactics are.
I'm John Kordis, and today I want to give you a look at What the Shell Cyberwarfare looks like. So let's dive in.
2022
I'm going to start this episode off with a couple small things. Firstly, I'm not going to be talking much about the physical conflict. This is purely a discussion on the cyber side of things. And while there may be physical ramifications in some cases, I won't be diving into the bloodshed currently happening. I don't want to subtract from that, but I'm going to stay in my wheelhouse here and try to stay on track and talk security.
Secondly, Russia is and always has been, pretty with the curve of cyber-attacks. So to do a thorough look at when they really started attacking, is a bit difficult because in reality, it's more like they never stop. They spread ransomware, launch denial attacks and propaganda attacks all the time. Some of it targeted at the Ukraine, and some of it targeted at us too. You'll see some of it this episode. So to make things easier, I'm going to limit the discussion to events in 2022.
Jan 11
Joint Alert warns of ongoing Russian state sponsored attacks.
I want to start by taking you back to one of the early indicators of something happening. For a little background I work in Vulnerability Analysis. There's a lot behind that but let's just keep it simple and say I help assess and remediate cyber risks. Well, as a part of that I have a process that includes keeping up to date with the latest government cyber intelligence that's publically available.
You see, CISA, the Cybersecurity and Infrastructure Security Agency, maintains a public website where you can monitor alerts, and current activity. You can go there right now and check it out if you want. There are tons of useful content for companies trying to keep secure, like lists of actively exploited vulnerabilities and even recommendations on free tools for enterprises that can't afford a largescale cyber effort. But I digress.
On Tuesday January 11th, I logged into work and was going about my day, and one thing came up as something to keep in mind from CISA. It was a Joint Alert from CISA, the FBI, and The NSA. The full joint alert is linked on my website in the transcript, but here are some bits and pieces of it that reflect where we were then. It's titled "Understanding and Mitigating Russian State-Sponsored Cyber Threats to U.S. Critical Infrastructure"
https://www.cisa.gov/uscert/ncas/alerts/aa22-011a
This joint Cybersecurity Advisory (CSA)—authored by the Cybersecurity and Infrastructure Security Agency (CISA), Federal Bureau of Investigation (FBI), and National Security Agency (NSA)—is part of our continuing cybersecurity mission to warn organizations of cyber threats and help the cybersecurity community reduce the risk presented by these threats.
CISA, the FBI, and NSA encourage the cybersecurity community—especially critical infrastructure network defenders—to adopt a heightened state of awareness and to conduct proactive threat hunting.
The went on to list three steps for organizations
- Be Prepared. Confirm reporting processes and minimize personnel gaps insecurity coverage. Create, maintain, and exercise a cyber incident response plan, resilience plan, and continuity of operations plan so that critical functions and operations can be kept running if technology systems are disrupted or need to be taken offline.
- Enhance your organization’s cyber posture. Follow best practices for identity and access management, protective controls and architecture, and vulnerability and configuration management.
- Increase organizational vigilance. Stay current on reporting on this threat. Subscribe to CISA’s mailing list and feeds to receive notifications when CISA releases information about a security topic or threat.
What this is saying here is that they're aware of an increased threat from Russian sources. Be on guard, especially if your organization might be enticing to them. If you need to, here are some steps to take and then they went on to list, a lot of technical details for organizations to block some of the known attack patterns.
This isn't too far off from unexpected honestly. These Joint alerts come out pretty frequently and in waves. There was already tension between Russian and the Ukraine at the time, and it seemed reasonable to expect a cyber response because that's just how it seemed to operate. But this was one of the first bigger pieces of awareness to come out about a large-scale issue forming. So, people started to put their guard up, operated in heightened awareness, and things would stay pretty much in the status quo for the next month or so.
Feb 15
So, let's bring it forward to February 15th here. It's been almost a month and at this point tensions between the Ukraine and Russia are only getting higher. There has not yet been a land invasion but there are indications that things are heating up on the cyber front. You see, on this day PrivatBank, which is the Ukraine’s largest commercial bank, was hit with a denial-of-service attack. There are many reasons why someone might go for a denial-of-service attack, but with the added aspect of the Ukraine’s Defense Ministry and Armed Forces websites also being disrupted, it seemed the clear indicator was that Russian actors were responsible for this.
So why would you want to do that? First, it sends a message. It's a warning flag that the cyber warfare game is one that's willing to be played and there are very real consequences if it's played tough. At this point I believe there were still discussions being had, and this would back some of what was facing Ukraine with the threat of losing capital. After all, this denial-of-service attack resulted in users not being able to access funds or perform online banking transactions for hours. This meant no money for normal citizens and would be a big blow to morale for a typical Ukrainian.
After a more thorough audit of their systems, there was evidence of hackers working for Russian Federal Security and their military spy agency, throughout the Ukranian networks. At this point, I’ve had people ask me before, well how would you know it's them? So I want to take a minute to talk about it.
At a high level, a lot of hacking can be broken down into tactics, which is how a hacker or threat might behave at the highest level; a technique, which is more detailed, and procedures. A tactic might be something like reconnaisance of a target or gaining that initial access. A technique would then dive deeper into that. A reconnaisance technique would be something like vulnerability scanning or phishing, and for that initial access it might look like gaining access to valid accounts on the network.
Then in the most descriptive side, there's procedures, and that's how that stuff is actually done. Do they use the credentials to try to make fake transactions if it's a financial compromise? or do they try to create persistent access? For reconnaisance, are they scanning from an external appliance, if so, which?
All of these, commonly referred to as TTPs in the industry, can be thought of as pieces of a fingerprint. Since it takes a lot of work to hack major organizations like this, things get reused quite a bit. It gives the attacker a bit of a playbook they can run through, but it also allows us, as defenders, to recognize these patterns and act accordingly. The MITRE attack framework offers a very comprehensive list of how these ttps can be mapped to certain groups and how they can be used in conjunction to get deeper into your network. I highly suggest you take a look at that too.
So, using the information that was available at the time, it wasn't officially confirmed yet, but it seemed probable that the suspect which took down the PrivatBank and Military website was Russian based, because of the tactics displayed and where the traffic was coming from.
Feb 18
Let's bring it forward a few more days here. On Friday, the 18th of February, it was reported more in depth that what was seen was a high volume of traffic, originating from Russia into Ukranian networks. What we talked about just now was the first phase of this attack but what followed that was spamming of SMS services. Effectively a scam. Thousands of Ukranian were getting messages on their phones saying that their bank doesn't work, and that the website it down. Now SC Media reported on this, and made a very solid point. This simple text accomplished two very important things.
The first was that, in general this was a scary message. If I received this text, and assumed it was valid, I would be worried about any transactions coming out and being able to get to my personal finances. So it stirred some unrest in people banking with the impacted companies.
But the second thing it did, was it added fuel to the fire. You'll remember if you've listened to past episodes that a denial-of-service basically is like trying to send too many requests at one time. So many, in fact, that the servers can't handle it and they just stop being able to take requests. Well, if you got this text that your bank was offline, how many of you might go check? Any of you that did, you'd be adding another request onto the pile. Some people might sit there refreshing, waiting to see if it comes back up so they can get to their money, and each time just silently contributing to the attack, not on purpose, just out of fear for their earnings.
Feb 23
We're going to bring it forward a bit more now to February 23rd. This is the day before the land invasions really started. So you can imagine how people are feeling. Things are about to break, and tensions are at an all time high. Now this all needs to come with the context that at the highest levels, the invasion was getting ready to go. While there's seemingly disputable accounts of people at the lower levels of the chain of command knowing, orders are coming from on high to keep with the cyber-attacks and things start to escalate a bit in the digital area.
Wiper Malware targets Ukrainian Enterprises
On Wednesday, a week ago as of this airing, at least two different private organizations were targeted by wiper malware. This was brought to the attention of the public by the technical director of Symantec Threat Intelligence. It didn't hit widely, only impacting a couple hundred machines, but it was enough to catch attention. Wiper attacks in this case are meant to disrupt. They'll utilize a legitimate vulnerability to squeak in and corrupt or wipe data from the host. Sometimes, if possible, it will also spread out where it can. So anyone who was impacted by this would not be able to use whatever was impacted and the system would need to be completely rebuilt. Imagine if the system was something for security, or financial transactions. How might things be ground to a halt here.
What's interesting about this, is that upon analysis of the malware, is was found that the code for it was compiled and built in the end of 2021, before any official announcement of the faux peacekeeping mission that would turn into a war. This has been taken as a clear intent of premeditation on the cyber front, and those six weeks were likely used to plan how they would get this malware in and when.
It didn't stop there. Because the next big concern came from risk centered around Ukranian Air Traffic Control. A warning was issued to airlines asking that they stop flying over the Ukraine altogether. What they were largely trying to avoid here was an unintended shootdown of a civilian airline, but the byline to this warning was that a cyberattack against air traffic control was not off the table. It seemed possible that with the ongoing attack, taking away the ability to control your own airspace was something that would be very valuable. To any planes in the air, though, that meant you could potentially lose any ability to coordinate you flight with airports. Imagine in this case, you've budgeted for fuel to one airport but suddenly you can no longer communicate, you then have to problems; a set amount of fuel before you need to land and no way to coordinate that against over aircraft in the area. It would be a major disaster if anything stuck in this kind of cyber-attack so the high level of concern was warranted here.
Sandworm Malware
The last major event on the 23rd came in the form of another Alert from CISA. This time it was a joint statement from the United Kingdom’s National Cyber Security Centre, the US National Security Agency, CISA, and The FBI. It was an alert for the public that threat actors called Sandworm, or Voodoo Bear, depending on who you talk to, was using a new malware called Cyclops Blink. The threat actor and exploit chain here was being attributed to the Russian General Staff Main Intelligence Directorate center for Special Technologies. That's a bit of a mouthful but it's just to say that they're government sponsored hackers and cyber staff.
The malware would root it's way in on the outer edge of a network, through the internet of things. Infecting stuff like routers and storage devices and allowing them to be used to accomplish further damage downstream. Once it got in through backdoor accounts that it was able to exploit, it tricked these systems into thinking there was a firmware update and would install a fake version. That allowed them to maintain persistence until a new update or complete reset was done. Victim devices here were then put into clusters and could be used as wanted by the enemy. This malware would further assist Russia in a level of cyber dominance, granting it more power to complete ddos attacks, or mask their attacks under the guise of traffic from a legitimate source.
Feb 24
It's at this point, when things have been turbulent on the diplomatic front, disruptions have been caused on the network space, and things are shaky that the ground invasion began. But, with this physical action, we also started to see counteraction against Russia on the cyber front. And because of the widespread condemnation of the invasion, people show up in force. Whether it's advocating a change in business as a sanction to Russia, hacktivists trying to do their own part to help, or the Ukranian government starting to turn out their cyber as a response. And there is a lot to turn out, even within its own borders. Did you know that Ukraine is one of the larger growing tech hubs in that part of the world? There are over 125 startups located there, and the IT Sector grew by almost 36% in 2021, annualizing nearly 7 billion USD for country.
With such a booming tech industry, there also comes with it the darker side of the internet for sure though. With technical capabilities for sustaining hacking operations, there was definitely a bit of a "hacker underground" if you will in the country. That's not surprising given that it happens in most countries anyways. But on Thursday February 24th, the Ukranian government saw this as an opportunity. After all, it was their home too. And this call to action was put out, not just to it's own people but to anyone that would listen.
"Ukrainian cybercommunity! It's time to get involved in the cyber defense of our country," and was posted but a co-founder of a Ukranian Cybersecurity company, allegedly at the behest of a top military official. It asked hackers and cybersecurity experts to submit an application via Google docs, and detail their specialties, such as malware development, and even went as far as asking for professional references.
The Ukranian government didn't officially comment but it made sense, given at as of the start of this year there was no dedicated cyber branch of their military, it was a weakness they knew they had but hadn't had time to start addressing yet.
Shortly into the day, things started to shift on the cyber side. There was retaliation from the world in the form of what appeared to be denial-of-service attacks against major Russian websites. Some of the sites that were hit included the site of the Russian president, the government infrastructure sites, and the lower houses of parliament. Similar to how PrivatBank was hit early on these sites would be down and inaccessible for several hours in one of the first major retaliatory cyber responses we would see.
It makes sense too when you think about. What have we said before about denial-of-service attacks? They're pretty easy to do if you've got the numbers. You plug in requests and point it at a target, and in this case because it's so easy I'd wager you can expect that to be the first line of cyber-attacks in a situation like this. There were probably a lot of low level hacktivists that may not have known where to start with an operation so they pick the big hitting sites for targets. It's a message, one that says "we have numbers too". It's not a heavy hitting enough punch to stop them in their tracks, but it let's them know you're there.
Meanwhile in the United States, President Biden addressed the world on the US's official cyber preparation here. Keep in mind, the United States has many different cyber arms. There are units in each branch of the military dedicated to cyber warfare and network defense. Playbooks have absolutely been written about how we can respond in this situation. So on last Thursday when Biden said quote
"f Russia pursues cyberattacks against our companies or critical infrastructure, we are prepared to respond. For months we’ve been working closely with the private sector to harden our cyber defenses, and sharpen our ability to respond to Russian cyberattacks, as well.”
He means it. And there has been a shift in the past few years. Defense officials haven't been exactly quiet about the fact that in the past a lot of cyber operations were aimed more in the offensive capabilities and response side of it, instead of defensive. So that's why if you look into stuff like Air Force Squadrons, starting in the late 2000's you might see redesignations. For example, the 33rd Information Operations Squadron was redesignated into the 33rd Network Warfare Squadron as new careers and missions started to fall in line with these goals.
So the US is, at this point, postured for a swift response if needed. I'd wager there are, for sure, operations going on that we don't know about but would be adamantly denied if probed on. That's kind of one of the sly things about cyberwarfare. Attribution is tough and denial is easy.
But what's interesting to me at this point, is that the Ukranian government began to lobby that the Biden administration cut off Russia from software updates for United States based software. This would be a big hit. Freezing their software that's in use at the time right now, means any new exploits or unpatched exploits are effectively kept open until they can build their own updates. It's not entirely unfeasible for that to happen but it's work they wouldn't have been counting on. It would give the whole world a bit of an edge because while there are alternatives to US software, it's still a huge powerhouse on the playing field. And at this point in the conflict, any advantage counts.
Feb 25
So here we're going to move into the next day. February 25th. That's Friday if you're keeping track. Offline, many are fleeing the country to seek refuge while the war wages on, and many are also staying behind to fight. It's important that I lay the groundwork here about people leaving for refuge because now we're going to see Russia start to hit back again on the Cyber Front.
Nations like Poland, bordering the Ukraine were opening their borders to let refugees in. And, in yet another attempt to slow people from leaving and decrease morale, attacks were levied against the Polish Government email systems and their systems that were used to clear financial payments. While Poland didn't officially attribute the attack to Russia here, at the very least it seems to coincide too well with what was going on conflict wise to ignore the relation.
The attacks were heavily monitored by Poland's leading power utilities because it was believed that the attacks went deeper than what was being found. However, the network remained operational with no disruption to power, which was a critical asset in being able to restore functionality if anything were to occur.
Following these cyber-attacks, Poland raised it's cyber security alert level, which would effectively prompt anyone that works with critical infrastructure to begin working more diligently on monitoring their systems for intrusion and compromise.
At the same time, Ukranian military personnel were starting to get phished for information with emails that prompted users to open links to compromised sites. Once visited malware would likely be levied against the mobile device or computer that opened it and give a gateway in for further intrusion by any bad actor. So the Ukraine Computer Emergency Response Team issues a warning to all personnel online that these were to be ignored and deleted. I have to imagine dispersing this information was tough because at the time network status must have been dropping in and out, information must have been coming from every side of them, and they're already dealing with the land war in front of them.
Another thing we've addressed in past episodes is that the Russian government does tend to have work done through third party cyber-criminal organizations. One such organization is the Conti Ransomware gang. Their name is pretty much an apt description of their operation. They develop ransomware and disperse it, leaking data and gaining bitcoin all the while. This gang, would come out in full support of Russia, saying on their blog that quote
"The Conti Team is officially announcing a full support of Russian Government. If anybody will decide to organize a cyberattack or any war activities against Russia, we're going to use all possible resources to strike back at the critical infrastructures of the enemy".
A pretty scary threat for sure, but one that does appear to have blown up in their face a bit. Because, and I'm skipping ahead a little bit here, but two days later an anonymous person decided to leak a whole lot of information on Conti. They leaked chat logs, which would reveal much about the internal workings of the group and these logs would go back as far as a year. The logs are currently not only helping security industries prepare defenses from the Conti ransomware gang, but they're offering a previously unseen glimpse into a chain of command between the gang and Russian intelligence agencies.
It's been unconfirmed, but the leak is allegedly from a Ukranian Security researcher that's been working their way into the gang, infiltrating it's operations masked as one of their own, while also making sure they were able to exfiltrate data. The person who did this, in my opinion, is a hero. This puts a big target on their back now, but it's a big win in the defense column. And that's how the Friday closed out in the cyber world.
Feb 26
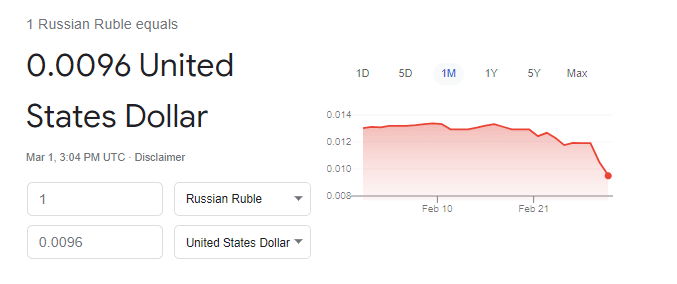
On Saturday, more sanctions and actions started to get kicked in against Russia, including the removal of their ability to use SWIFT. You might have heard of SWIFT in recent conversations but if you don't know, it stands for the Society of Worldwide Interbank Financial Telecommunication. Essentially, if you want to trade financially and internationally, or make payments between banks worldwide, it's done through this. So to do this, cut them off, was to essentially exile the Russian economy from most of the world. This was met, with uproar from the Russian government but there ultimately wasn't much they could do about it, and in fact their stock Market didn't even open today, February 28th. The value of the Russian Ruble is currently down to record lows, with 1 American Dollar being worth 105 Rubles.
In fact, it's fallen so far in value that in US Dollars, currently the Roblox videogame currency is worth more than the Ruble. This is what these kinds of sanctions are meant to do though, apply pressure without physical action because now, for better or worse, all of Russia is feeling this.
On the Ukranian front. Internet connectivity has been intermittent, and poor at best at this point. There are problems in the southern and eastern parts of the country maintaining connectivity because of the fighting going on there. You have to imagine that network lines are being destroyed one after another and there are only so many failovers that can be had before it's just done.
In a bid to help maintain access to the outside world, Elon Musk did something that I think is worthy of a little bit of praise, and he sent SpaceX Starlink satellite broadband terminals to the country to let them maintain their access. Starlink is satellite internet program launched under the SpaceX arm that aims to one day have global capabilities. By sending these terminals out there he's enabling fighters to keep dispersing information, keep fighting back on the cyber front, and keep the world aware of what is really going on. Because as much as a cyber war is about exploits, it's also about information. If Russia can cut off the information flow out of the Ukraine, then they'll control the narrative. Stopping that from happening is a critical part of this fight against propaganda.
The other big thing happening at this time, is that we're starting to see a pretty large response to the call to arms for cyber professionals. It's incredible to see the response that the security industry has shown here. For example Grey Noise, a security company aimed at collecting and analyzing data on attack activities immediately upped every Ukrainian subscription to VIP free of charge, to let them make use of the full capabilities of the tool in defense.
I'm linking a google doc at this point on the website because one twitter user is also amalgamating a list of tools that are now free to Ukrainians
https://docs.google.com/spreadsheets/d/18WYY9p1_DLwB6dnXoiiOAoWYD8X0voXtoDl_ZQzjzUQ/edit#gid=0
Nearly 100 different products which previously had cost money are now to include capabilities like better VPN, Offensive operations, DDoS Mitigation tools, premium threat intelligence feeds, and more. They asked and our community answered. I think because at the heart of what drives a lot people in this field, is the want to be able to contribute and to help defend. And when we see someone tearing down it's in our nature to want to stop it.
Meanwhile, in the US, our government issues something that I previously hadn't seen before, a "Shields Up" notice. That CISA site I told you about early on, they published this whole new page aimed at helping organization get into a better state of readiness. Stating that quote
"While there are no specific or credible cyber threats to the U.S. homeland at this time, Russia’s unprovoked attack on Ukraine, which has involved cyber-attacks on Ukrainian government and critical infrastructure organizations, may impact organizations both within and beyond the region, particularly in the wake of sanctions imposed by the United States and our Allies. Every organization—large and small—must be prepared to respond to disruptive cyber activity."
CISA, at the time of writing this, is asking all organizations to adopt a heightened sense of awareness. They're effectively saying to set the watch dogs out, and maintain vigilance because while there aren't any specific credible threats to us, it's not unlikely there won't be attacks. Especially, given the financial sector cutoff that's been seen so far. Retaliatory measures are always easier cyber-wise comparatively, so it's more likely that the first wave on incidents may be retaliatory to specific sanctions.
This shields up notice, like it said is meant for all organizations, and since not every organization can afford a full program it lists out major free tools that can be used to help keep readiness up.
https://www.cisa.gov/shields-up
Lastly, on the 26th, Anonymous got involved. That's the same anonymous hacking group that I talked about earlier this year. This time, Anonymous seems to have come out in full force. It started with DDoS attacks, as it always does, targeting State run media. This was their attempt at blocking Russian propaganda from being dispersed, which was seemingly pretty rampant. Additionally, they claim to have hacked the Ministry of Defense database and Russian state tv channels. The latter of which, you can actually find video of online on social media. State TV channels were hacked to play the Ukranian anthem and patriotic songs, and show actual footage of the conflict, so as to inform Russians of the true cost of what was going on.
They went on to release this video, which I've tried to edit down a bit because there was a bit of filler music that didn't really serve a purpose.
If this truly was anonymous, then I have to say this is probably one of their more impressive hacks to date. And yeah, Putin isn't going to surrender because of Anonymous. I don't think that was ever expected even from the person that made this video. But, it's more pressure tacked on and while I'm sure this video is largely a stunt aimed at intimidation, there a bits that back it up, and even a shred of good intention and action here offers more than doing nothing.
And we're coming up to the date that I'm recording this now. It's the morning of March 1st. At the end of this weekend, two major things of note happened, both revolving around the information side of the cyberwar. On Sunday, to prevent inaccurate news from being spread Google blocked the Russian state owned news apps from being downloaded in the Ukrainian territory. And just this morning, I read an article that Meta, previously Facebook, has found and addressed hundreds of fake accounts that were posting propaganda videos. The videos were fake scenarios of alleged Ukranian Soldiers laying down arms and surrendering, aimed at lowering the morale and inciting the idea that surrender was inevitable. The accounts have been removed and the issue addressed, but I doubt it's over. We've seen the capabilities the Russian social media machine in the past, they had a heavy hand in spreading false information during the 2016 and 2020 elections, and now we're seeing it put to action for a different cause. I'm not sure what the next strategy will be there, but they're absolutely working on it.
So that's where we are as of now. I hope I was able to give you a good glimpse into the idea that the war being thought on the ground isn't just all there is, that there's a war going on in the cyberspace too. There's more cyber-attacks going on day by day. Targets ranging from fuel depots, to individuals with connections to the government. It's not going to stop, and while there's not necessarily a direct loss of life correlated to these attacks, there is impact.
I want to end this episode on, an optimistic note. A close friend of mine put it well recently, telling me that yeah, there's terrible stuff going on in the world, but there's hope too. You just need to look. The security industry has shown up in full force. Black hat hackers, anonymous, security researchers, all trying to do what they can. On the ground, we have nations opening borders, waiving visa requirements, offering support like nothing we've ever seen.
So in lieu of my normal ending stinger. I want to only point you to my website. Whattheshellpod.com. In the episode transcript there, and in the description on the podcast episode I've put links for several donation sites that could use some help, taken from the Washington Posts coverage on where Americans that want to donate can do good.
https://voices.org.ua/en/donat/
https://donate.wck.org/give/236738/#!/donation/checkout
https://razomforukraine.org/donate/
I'm John Kordis, and I hope you learned a little bit about What the Shell Cyberwarfare really looks like this week. We'll be back in two weeks, thank you.