For the tenth episode, we're diving into the man that played TJX, Dave & Busters, and even the Secret Service for fools. We're talking about...the soup nazi.
Follow me on twitter and Instagram @shell_pod , email me at shellpod@protonmail.com , and check out the new site at https://whattheshellpod.com
Whether you're on a forum, playing games online, or even just setting up your instagram. You've probably got an online handle, a gamertag, a username?
Me… I go by the name Doc Hobb, it's shortened from its roots a bit but it's stuck with me other the years. It's my youtube handle, it was my gaming username of choice, and personally I think it was a fun way to give some character to who you are when you're online. Especially back when the number of places you could have a handle was a lot more limited, it just seemed a bit cooler. After all, in all the movies the hackers all had really cool usernames. Zerocool, Neo, Trinity, Blaze. Today I'd like to talk to you about Albert Gonzalez, who went by the alias "SoupNazi". A far cry from his Seinfeld counterpart, Gonzalez would take the name to criminal heights throughout the years, accomplishing some of the largest financial hacks to date.
My name is John Kordis, and this week on What the Shell? We're going back to the 2000's to follow the trail of the elusive SoupNazi and find out what secret recipes he's hiding up his sleeve.
Intro
Before we get into what he did, let's set the backdrop of who Albert Gonzelez, the Soup Nazi was. His father, Alberto, came to the United States from Cuba, in a raft that was made by hand, in 1970. He was seeking a better life, and would eventually land as a landscaper outside of Miami, marrying and having a daughter. Then, in late 1980, they'd get the news that they were having another baby, this would turn out to be Albert who would be born the following June.
His childhood would turn out to be fairly mundane. He'd enjoy childhood, and as he grew up to find his own interests, it would become clear that he had a fascination with computers. At just 8 years old he'd get access to his first computer and in an interesting turn, it would get a computer virus.
I don't know about you, but if my computer got a virus, I'd probably get a little frustrated, run my anti-virus tool, and do some work to try and make sure that I took care of cleaning things up. Little Albert, however, didn't have access to these tools at the time, and he was just a kid. Instead, he got a bit spiteful, and decided to dedicate his time to learning everything he could about his computer, to make sure that it didn't happen again. It wasn't a bad strategy, but you need to remember that at this point computers looked and behaved very differently than they do now. He wouldn't be able to just google something to figure out how it worked, it took some legwork to really get into the nitty gritty about how this device did everything he loved.
He'd continue to self-teach himself the ins and outs of computer architecture. This likely included learning how to code, what tools were available, and yes through these concepts, he would learn how that virus that first took him out worked. It's a pretty natural progression, but one that's all the more impressive by the dedication that must have gone into it. According to his high school transcripts, he never even took a computer class there, and he didn't go to college either. So literally everything he knew about this subject was self-initiated.
So, while not really taking the traditional route here, he managed to queue himself up for a decent work life, even landing himself a job in New Jersey firm right after he graduated.
Things would continue to remain fairly low profile for Albert until around 2003.
2003 arrest - and shadow crew
So let's jump forward to 2003, when Gonzalez would be caught doing something relatively minor in the kind of cyber crime we talk about, but that would have a major ripple.
It was July, and the SoupNazi went to an ATM late one night to start taking out cash. More specifically, it was just before midnight. When he got to the ATM, he wouldn't take out his own bank debit card though, he took out what looked like a blank card with a stripe on it. He used the card, entered the pin, and withdrew as much as cash as he could. Then…he took out another, and did the same thing. He'd do this a couple times, wash rinse repeat, until he ran out cards and had taken out as much cash as he could. This is where the "Close to midnight" comes into play. At midnight, the cash limit for the day resets because it was tied to the date and not a specific 24 hour period. Do you see where this is going? Gonzalez was now able to double dip. Once that midnight line was crossed, he could just start over and save himself a lot of time the next day, plus double the money he had provided the account was filled enough. These cards, weren't his though. SoupNazi had a pack of stolen cards that he was milking one by one till he was out. The double dipping would help here because it was entirely possible if he waited the card numbers might get canceled. So he had to act quickly, or lose the opportunity.
I want to let you know, it's incredibly easy to clone a credit card if you have the right data and tools. An easy way to do this is to simply scan the card, using something like a fake transaction reader. These can even be disguised to look like something real, for example one can be put over a gas pump or an atm card insertion spot. They'll look just like the real thing and unless you accidentally pop it off, you'll be none the wiser. If you'd like to see one, I'll have pictures on my website and on instagram showing you how real they can look. It was such a problem, in fact, that I remember in the mid to late 2000's when daily news would have special alerts to be on the lookout in your area because some of these had been found. These days, with the chip technology in our cards, it's become a bit harder for this kind of attack, but before this really took, it was an incredibly easy thing to do.

The other thing you might be able to do, if you knew where to look, was buy the card information yourself online, and program the cards yourself. This, is what Gonzalez did. But where did he get that info? A site called "ShadowCrew.com"
Gonzalez had started to make his way down toward the path of a more black hat in the cyber way. Gonzalez spent a lot of time as a moderator on that site. It was a bit of a haven for hackers and fraudsters with stolen data or goods that they wanted to offload for a bit of a payday. Not only that, it also specialized in the sale of drugs. It was a precursor to sites like SilkRoad and Alphabay.
In 2003, pre my-space and social media as we know it, 4k members was a massive community. It was natural that they would need talented and savvy people to help moderate it, so Gonalez, who at the time went by the handle "CumbaJohny", assisted in that effort. Normally, the site would be hosted in Hong Kong. This kind of helped in a way similar to how we've talked about Russian sites being operated. It was a lot harder for the US to get it taken down if it was hosted off shore. But because he was an admin for it, shortly before this night in 2003 he had a copy of the server set up in his possession….In New Jersey.
So on this night in July, in 2003, when a detective noticed that Gonzalez was up to some shady stuff and decided to bring him in? Gonzalez didn't realize it yet, but he'd have quite a bit of leverage.
At this point we're going to move out over to the Secret Service. Yes, the secret service like the group that guards the president. The secret service has more than just that mission, in fact they are a critical group for investigating cyber fraud. And in 2003, they launched what was called "Operation Firewall". Until then, there hadn't really been largescale operations against ogranized cyber crime. So it was still fairly new ground. They just knew that there was a problem with fraud, namely stolen payment data and it needed to be addressed.
Well, imagine this, you're a Secret Service agent brought in on this local guy who's got some digital credit card fraud going on, in the midst of operation firewall. What do you do? I think you cut him a deal to get him to lead up to some bigger fish. After all, Gonzalez was looking down the barrel of a 20 year prison sentence at just 22 years old. He'd lose some of the best years of his life if he didn't cooperate so the decision was a bit of an easy one to make.
He'd cooperate with the Secret service and it would lead to the takedown of the shadowcrew site. From their userside what they would see is a completely funcitonal site until one day….it looked entirely different. One day they'd browse to it and thind this message:
"For those who wish to play in the shadows" Activities by shadowcrew members are being investigated by the United States secret service. Several arrests have recently been made with many more to follow. Proxies, VPNs, IP Spoofing, Encryption. You are no longer anonymous. Shadowcrew members are facing the following charges and then it listed Conspiracy, Access device fraud, fraud with identity documents, identify theft, and more. If you are a member who is confused and/or concerned by your actions please read the following. Recent news reprots should inform you that the secret service is investigating your criminal activity. Contact your local United States secret service field office. before we contact you.
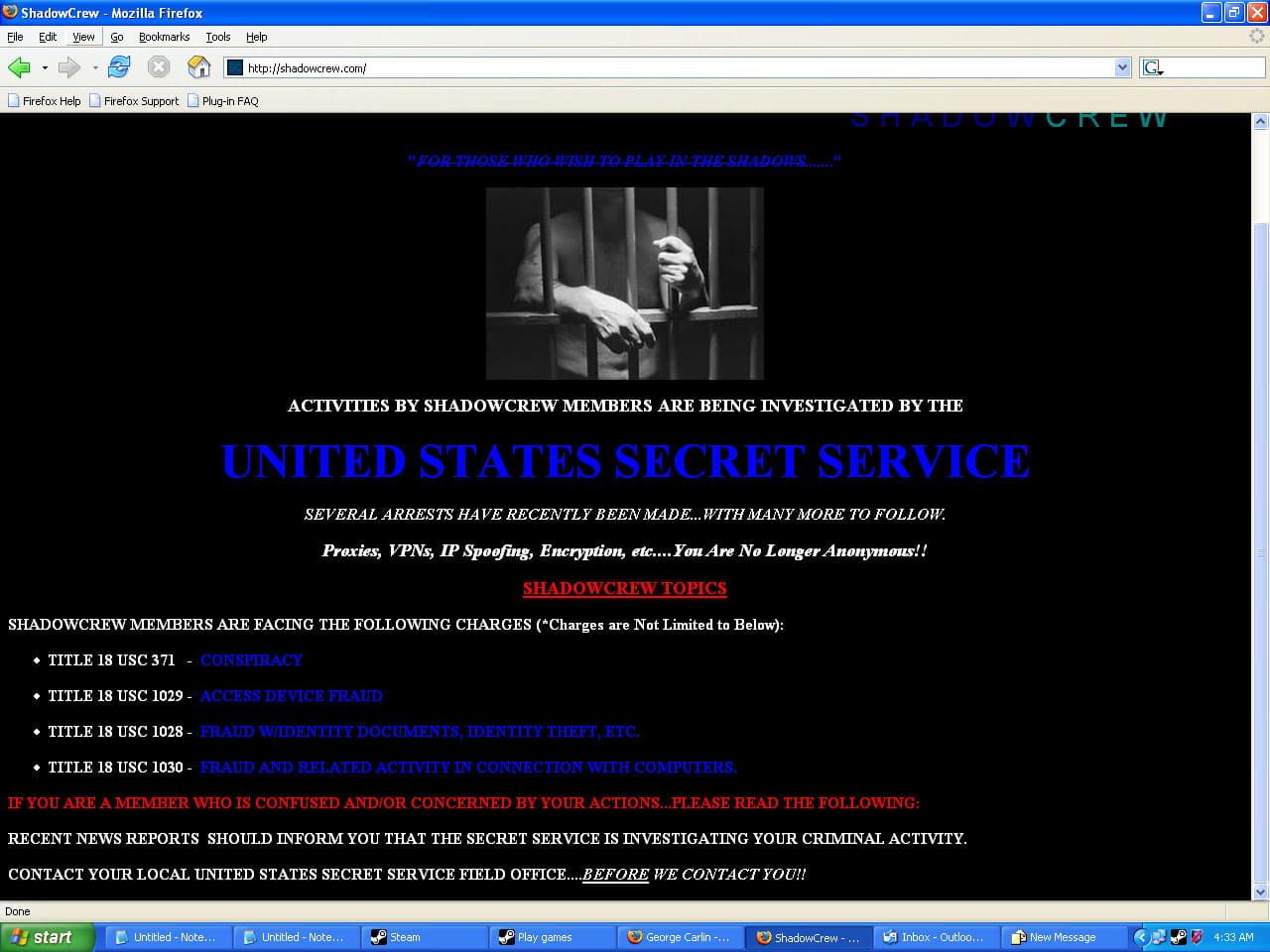
Looking back at it, it's actually pretty funny to me. The site looks like it was designed by a middle schooler learning html, and they put on this big intimidation tactic to try and get users to come to them. Admittedly it would work on some levels, but just looking at the site with the hindsight we have now, it's bizarre.
So for the next few years the feds would help Gonzalez kick his drug habits, and even front him on a place to stay for part of it. All while Gonzalez was feeding informaton that was getting them big busts. Some of the agents who worked with him even noted that while he was relatively introverted at first, once he opened up there was a certain charm to him that many found endearing. According to records, he'd end up getting around 75k a year to do this kind of work over the next few years. And from the outside in, it genuinely looked like he was turning his life around.
But….while the Secret Service was moving on from Operation Firewall, thanks in large part to Gonzalez, the SoupNazi himself decided to launch his own Operation. He, and the group he'd work with would call it "Operation Get Rich, or Die Trying".
Much the social engineer, Albert was playing the feds. While he was helping them, he was still at his old games, but this time he had it cranked up to 11.
It all started in 2005, with something called "War Driving". War driving, is a pretty simple concept. You get some beefy wireless anetennas, put them in your car, and drive around documenting what you find. You might find open wireless networks, or networks that are running on vulnerable hardware, you also might find something in the way of weak encryption.
Think of it almost like you're walking down a beach dragging a shovel. You're catching a lot of sand in the shovel, but in there might also be valuables, shells, or something interesting. All you need to do is sift through it, and you might have yourself something good.
By default, we all usually broadcast our wireless networks, so in this case they're the sand. But fortunately, we're also usually well protected. It's the those weak ones we talked about that are the loot here.
And one such piece of loot was pretty interesting. It was an unsecure network outside a TJX outlet.
This was the first step on his journey though. With the foothold in place, he pivoted all the way to the corporate network, located in Western Massachusetts. He'd made some good progress, but he was walking on thin ice here. He needed to be quiet or risk losing everything he'd been working toward.
But Gonzalez had an in, and went to his long time friend and occaisional accomplice, Stephen Watt, who was a coder. He asked Watt for a tool he could plant on the network to sniff around for anything from transaction data to passwords. And Watts provided, he called the tool "blabla".
Using blabla, Gonzalez would be able to capture credit and debit card numbers as they were processed and was able to either use it or sell it as he saw fit. He planted the sniffer, and sit back and let it do it's thing.
TJX wasn't the only place he'd be able to get his hands into though, blabla would eventually be found not only there, but in places like Dave & Busters the following year. All in all, SoupNazi would make out with the information of over 130 million credit and debit cards.
There was still the problems of the feds though. He couldn't just sell it, he was still under some level of scrutiny because he was still feeding information to the secret service. So he created a routine that worked in his favor.
SoupNazi went and leased servers offshore, located in the Ukraine and in Latvia. The stolen card data was routed there first. Once there, a card seller by the name of Maksym Yastremskiy would in turn get them out to the larger underground group of people in the business. The would program the card data, get what money they could out of it, and then it would be laundered back to Gonzalez. It's estimated that Maksym himself earned over 10 million in this operation. So it standas to reason that Gonzalez, made a pretty penny for himself.
Gonzalez's game here was to stay as low to the ground as possible though, which is why he had this operation set up so far away from him. He couldn't remain entirely out of the picture though, so he adopted a new alias. No longer the SoupNazi, he'd now go by segvec, that's s-e-g-v-e-c. As segvec these criminal activities he was putting under his belt were orders of magnitude greater than anything he'd done before. He was using his earnings pretty loosey goosey too. Some of the items he'd paid for outright included a condo, a bmw, some pistols, a diamond ring, multiple rolex watches, and more. How some of this went unquestioned is beyond me. He must have been doing a really good job covering his trail to not alert the authorities that he'd suddenly start coming into some big money.
But while Albert had gone relatively unnoticed, the same couldn't be said for his alter-ego segvec. Then again, I guess that was the point. Segvec was on the governments radar but they had no idea he was their own informant.
As it seems the ones that get caught always do, segvec would maybe get a little too careless. At this point the feds were clued into some of these hacks, including the Dave and Busters one. And internet chatter would give them a clue that they were having trouble maintaining their persistence in the D&B network. Anytime the systems shut down, it would need to have the malware reintroduced to keep working. That started the chain the eventually led to the ultimate conclusion: segvec was Gonzalez.
And as the twine was unwound, this group that was operating under the name of "Project Mayhem" was identified individual by individual.
Remember Stephen Watts? He was charged for writing that sniffing malware that helped facilitate all this. He's end up getting 2 years in Jail and needing to pay an amount of 171.5 million dollars to TJX for his role. How do you even start that?
I want to pause here for a second though. If the name Stephen Watts sounds familiar, it's because he was breifly mentioned in a past episode. You might remember his internet alias "Jim Jones", or JJ. If you don't or you haven't listened to my episode on him yet, this is the same JJ alias that led federal agents to think that "Jonathan James" was connected to these hacks. Ultimately resulting in him taking his own life from being, how he saw it, scapegoated for this.
For Gonzalez though, he'd not get off as lucky. On August 28th, 2009 the attorney acting on behalf of Albert filed papers with US District Court for Massachusetts that showed he would plead guilty to all 19 charges that were brought against him and in March of 2020 he would be senteced to 20 years in prison. The list of hacked companies he was charged for included "TJX, Office Max, Dave and Busters, Barnes and Nobles, and more". To add insult to injury the very next day he received another 20 year sentence for hacking Heartland Payment systems at the same time all of this was happening. Luckily for him, as a part of the plea deal he was able to serve those two sentences concurrently, meaning he would serve 20 years total.
And that's what he's currently up to. He's down in Kentucky at the Federal Medical Center, a prison in the area. A few years after his sentencing he tried to take back the guilty plea because he hadn't been informed that he could use a public authority defense, since he'd been working with the secret service at the time, but that doesn't seem to have really gone anywhere. After all, it's a little hard not to think of him as guilty when before he was sentenced he was quoted as saying to the court that he deeply regrets his crimes, and is remorseful for having taken advantage of the personal relationships he'd forged. "Particularly one I had with a certain government agency ... that gave me a second chance in life. I blame nobody but myself".
He's got just 3 and half years or so left in his time in jail and he'll be in his mid forties. He hasn't had much access to computers, only being able to use them when his lawyer comes to visit and review evidence, but I'm curious as to what he'll get up to when he's out. He's got plenty of time to make a positive impact in the field, or maybe turn back to his old ways. Either way it should be interesting to see.
I'm John Kordis, and thanks for taking the time this week to listen to me explain What the Shell the SoupNazi did, and why he's still in jail for it. But before we go, I wanted to put a call out to you, the listener. Do you have interesting stories from the hacking community? Are you an expert in the field? I'm interested in expanding on the interview format I did a few weeks ago with Tank and I'm looking for people that might be interested in sharing. If that sounds like you, you can head to my website whattheshellpod.com. There you'll find a contact page, where you can send me a message. Let me know what you've got and if I think we can use it in an upcoming episode I'll gladly try to get it together.
Even if that's not the case, I'd like to encourage you to visit the site anyways. You'll also find links to our various social pages including our discord channel where you can come and discuss episodes with me and others In the community. As well as the episode script and reference images I talk about.
If that's not your cup of tea, you can always follow me on twitter or instagram @shell_pod. I'll see you in two weeks with the first episode of 2022.
-----

